Every time you buy something online, you put your faith in math – simple math that’s easy to do in one direction but difficult to do in reverse. That’s what protects your credit card information from would-be thieves. But the system can be hacked.
One popular encryption scheme, for instance, can be undone only by factoring a huge random number, a “key” unlocking encoded information, into two prime numbers. It’s a task that today is extraordinarily difficult, but not impossible. With enough computing power, a spying government could break the key. Or some clever mathematician could find an easy way to factor large numbers and do it tomorrow, in theory.
In search of greater security from code breakers, a new generation of code makers has been turning from math to physics. Experts in atoms and other particles, these cryptologists want to exploit the laws of quantum mechanics to send messages that are provably unhackable. They are the architects of a new field called quantum cryptography, which has come of age only in the past few decades.
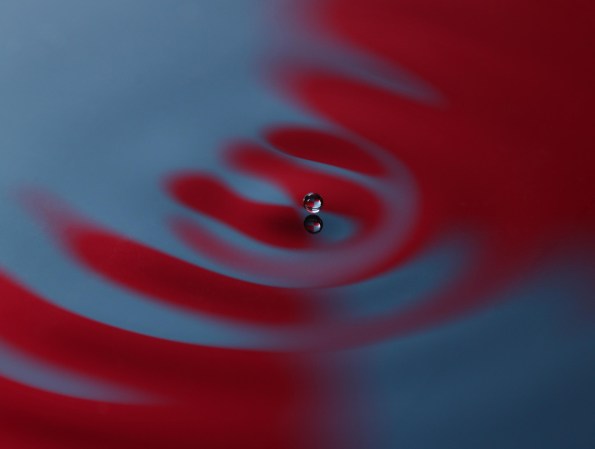
Quantum cryptography draws its strength from the weirdness of reality at small scales. The particles making up our universe are inherently uncertain creatures, able to simultaneously exist in more than one place or more than one state of being. They choose how to behave only when they bump into something else or when we measure their properties.
Quantum cryptography draws its strength from the weirdness of reality at small scales.
The most popular cryptographic application yet for this strange behavior is quantum key distribution, aka QKD. A quantum key encodes and sends the information needed to decrypt a message in the fuzzy properties of particles, typically light particles. Eavesdroppers trying to steal the key must make measurements of those particles to do so. Those measurements change the particles’ behavior, introducing errors that can be detected and alert users that a key has been compromised and should not be used to encode information.
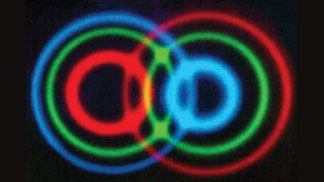
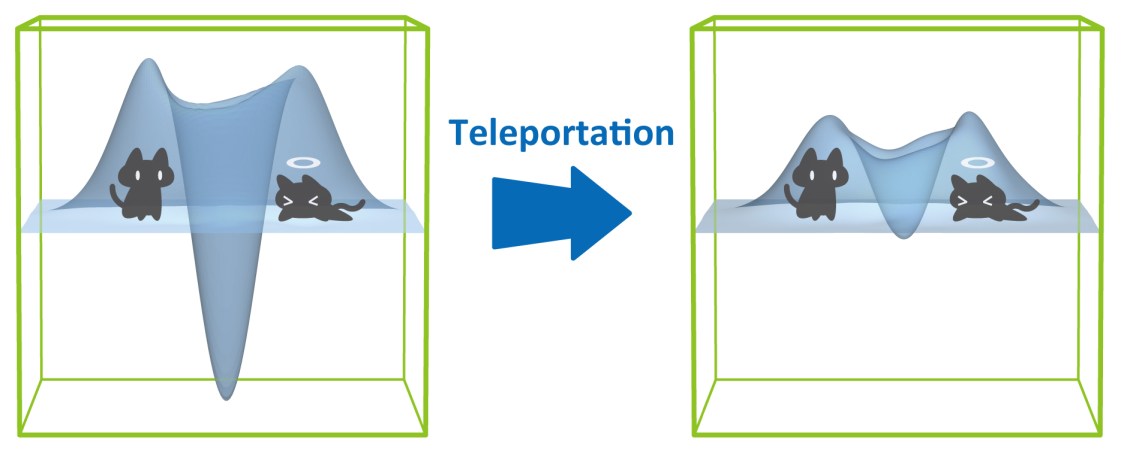
Many variations on QKD exist, some of which employ an unusual long-distance quantum connection called entanglement to protect information. Entanglement allows two particles to behave like a single entity, no matter how far apart they are. Meddle with one particle, and its partner instantly reacts, even at the opposite end of the universe, revealing the presence of a hacker.
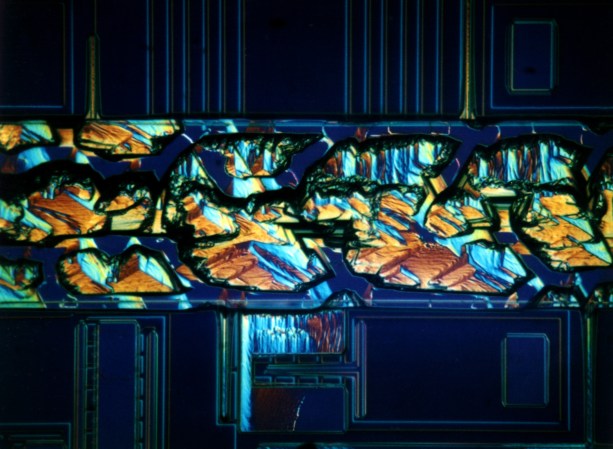
QKD systems are becoming a reality. The first quantum transaction took place in 2004, when researchers in Vienna used entangled photons to transfer a 3,000-Euro deposit into their bank account. Commercial QKD systems came to the United States in 2013, when R&D nonprofit Battelle installed a fiber optic network protected by encrypted photons. The system, developed by ID Quantique, had already used its technology to protect the results of an election in Geneva in 2007.

“There is still a way to go before it becomes a standard commercial proposition, but we are getting there faster than I expected,” says quantum cryptographer Artur Ekert, a professor at the University of Oxford and director of the Centre for Quantum Technologies at the National University of Singapore.
Meddle with one particle, and its partner instantly reacts, even at the opposite end of the universe, revealing the presence of a hacker.
Entanglement can allow for extra security compared to other QKD schemes. While the latter requires the device being used to be trusted, entanglement opens the door to device-independent cryptography that remains secure even on untrusted equipment.
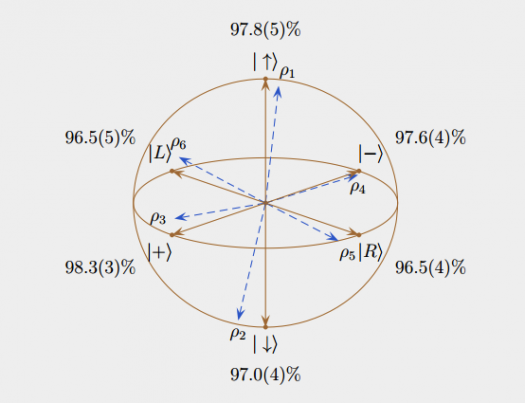
The quantumness of an entanglement-based system, which guarantees its privacy, can be verified using a set of statistics that describe how similarly the particles behave, called Bell inequalities.
And while QKD has become nearly synonymous quantum cryptography, it is only one of many ideas in the field in various states of development. In the 1960s, a professor at Columbia University developed the idea of a quantum money that would impossible to counterfeit; each bill would house trapped particles whose properties could be verified by banks. And quantum random number generators can now spit out numbers based not on computer algorithms, which can never be truly random, but on really random quantum fluctuations.
Others are working on secure ways to send tasks from a normal computer to the quantum computers of the future – devices that promise to be better at certain jobs than today’s computers – among them, ironically, the factoring of the very large numbers protecting your credit card transactions today.
The future of code makers and code breakers is entangled, and it may be quantum on both sides.