Every group of friends has that one person to go to for tech advice: what kind of TV to buy, the right HTML tags to pimp out a MySpace page, and so on. Believe me, I would know. But although I consider myself fairly willing to share the tech wealth, my powers pale in comparison with the sage wisdom dispersed in the “Ask a Geek” feature found in each issue of Popular Science. Every month, we feed the practical questions faced by everyday netizens to some of the web’s brightest minds—including Gina Trapani (editor of Lifehacker), Merlin Mann (editor of 43 Folders), Jake Ludington (keeper of the MediaBlab blog) and Annalee Newitz (tech writer extraordinaire, Second Life whiz)—anything from ridding your computer of spyware to using any song file on your computer as a ringtone.
But that’s only the beginning. Here we present a compendium of the choicest nuggets of nerdy advice—get yourself a geek education.
And if you have any wisdom of your own to share, or perhaps a question for our geeks, we want to hear about it over on the How 2.0 blog.
Table of contents
- How do I hang my flat-screen TV? by Bryan Greenway
- How (and why) should I encrypt my data? by Gina Trapani
- Can I download streaming videos off the web? by Jake Ludington
- Can I plug In my Prius? by Stephan Wilkinson
- Can viruses attack my cellphone? by Eugene Kaspersky
- How can I make a personalized email address? by Merlin Mann
- How can I surf the web anonymously? by Annalee Newitz
- How can I guard against spyware? by Ben Edelman
- Can I use my own songs as ringtones? by Gina Trapani
- What music format is best? by Jonathan Coulton
- Why do batteries explode? by Nicole Dyer
- Is the music industry still suing people? by Fred von Lohmann
- Can I wipe my name off the web? by Lauren Gelman
- How can I tame my overflowing inbox? by Merlin Mann
1. How do I hang my flat-screen TV?

Maybe you don’t. Ask yourself if you trust your handyman skills enough to wager your new $2,000 LCD on them. Not sure? Hire a pro. It will cost $150 or more, but that satisfaction you get from a DIY job fades quickly when the set is in pieces on the floor.
If you do decide to proceed on your own, check your TV for the words “VESA compatible,” which means it’s designed to work with standard mounting hardware. I stick with two bracket brands: OmniMount for sets smaller than 37 inches, and Peerless for anything bigger; prices start at around $60. Spring for one with tilt to reduce glare.
When deciding where the TV will go, know what you’re getting into—literally. Find a spot on an interior wall, out of direct sunlight, with at least one stud to anchor an LCD, or two for a plasma. Use a stud finder to check for obstructions in the wall. That’s important, because the secret to a clean, “floating” installation is to run your audio and video cables behind the wall and pull them out down by the floor, nearer your receiver. Include an extra set of cables so that you can add components later without taking down the TV.
Mount the wall bracket with heavy-duty anchor bolts (don’t forget to use a level). Get help hanging the set, no matter how small it is. Close the safety tabs around the rails, and you’re done. Except, of course, for explaining to your friends how you made it look so good.
Bryan Greenway is a professional installer and editor of hometheaterblog.com.
2. How (and why) should I encrypt my data?

With files constantly on the move through USB drives, online storage sites and multiple email accounts, your financial records, password list, and secret barbecue-sauce recipe are more susceptible than ever to being stolen or simply lost. But that doesn’t mean your personal info has to be spilled to the world. Several free tools make it easy to scramble your files so that even if someone cracked them open, they would look like gibberish.
Free Windows software fSekrit (donationcoder.com) locks down text documents and saves them as EXE files. That means you don’t need fSekrit to open them again, which makes it a good choice for emailing files to someone else. And at 40KB, it’s easy to keep on a small USB hard drive. For saving multiple files, TrueCrypt (free; truecrypt.org; Windows) creates an encrypted virtual hard drive on your desktop. Save as much as you want in it, then “dismount” it. The drive can’t be remounted without your password.
Mac users have a similar function built in. Open Disk Utility and create a new disk image with the encryption style of your choice (all are equally effective). A final reminder: Even encrypted, your data is only as safe as your password. Choose one that´s long and hard to guess, and change it often.
Gina Trapani shares productivity tricks, time-saving websites, and useful software every day as editor of the blog lifehacker.com.
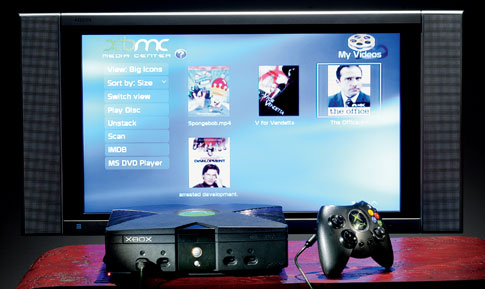
3. Can I download streaming videos off the web?

Most of the movies on sites such as YouTube and Google Video are the sort of flicks you’re happy to watch once and forget about. But occasionally, there’s that hilarious gem you just have to keep for repeated viewing. What’s limiting about these sites, however, is that the movies play only in your browser. This makes the videos widely accessible—no special media player needed—but it also means you’ll need another tool to download and save them to your computer.
My current favorite is KeepVid. Visit keepvid.com, paste in the web address of the page with the video you want to save, and KeepVid will find the file and give you a link to download it. If it’s a YouTube file, you’ll need to add the extension .flv when you save it. You’ll also need an app to play FLV files, such as FLV Player (free; martijndevisser.com). Is it legal? Depends on the video. Most home movies are in the clear, but downloading an episode of South Park could violate copyright, since it was probably posted without the owner’s permission. So far, people have been sued only for redistributing files, not downloading them, but to be safe, don’t assume that everything out there is ripe for the saving.
Jake Ludington runs MediaBlab (jakeludington.com), a blog of tech tutorials.
4. Can I plug in my Prius?

- The short answer: Why bother?
- The shorter answer: Why not?
Toyota says the Prius is neat because you don’t have to plug it in—it charges itself when running on gas. But what if you could plug it in? If you could fully charge a set of supplementary batteries overnight from household current and do the next day’s errands purely on volts? (The gas engine will stay off under 35 mph if you have enough battery life and you’re gentle on the throttle.)
CalCars, a California eco-car consortium that has converted a handful of Priuses to plug-in models, is about to issue a free do-it-yourself instruction dossier with photos, a video and a shopping list of all the components you need. The hardware will cost you about $3,000, a third of it for a trunkload of lead-acid electric-bike batteries (so Costco runs are out). It’s not a weekend project, but anyone comfortable working with high voltages can do it. The mod won’t void your car’s warranty entirely, but don’t expect the dealer to help if you screw it up. So for the price of a perfectly good used Corolla (plus the Prius’s $22,000 price tag), you have a plug-in hybrid that can take a trip of less than 10 miles on electricity alone. But you can still go as far as your gas engine will take you—averaging as much as 100 mpg, according to CalCars. Is it worth the bother? That’s up to you.
Stephan Wilkinson is the contributing auto editor at Popular Science.
5. Can viruses attack my cellphone?

If it’s a smartphone, you bet. In 2004, virus writers released Cabir, the first proof-of-concept virus that could infect smartphones through an open Bluetooth connection. So far, Cabir and the 175 other smartphone viruses in the wild haven’t done enough damage to warrant headlines. But it’s only a matter of time before there’s enough financial up-side for criminal hackers to begin seriously attacking smartphones. And then, watch out. No smartphone? You’re still not safe. A scam now common in Europe involves sending text-message spam that pretends to be a missed-call notice. Return the call, and you’re unwittingly charged several dollars, just as if you’d called a 1-900 number. A similar threat uses malicious code embedded in an innocent downloadable game. Once loaded, it secretly sends multiple text messages to costly premium numbers. Here’s how to protect yourself:
- Never text or call back numbers you don’t recognize.
- Don’t open unknown attachments or follow links from an email.
- Turn off WiFi and Bluetooth connectivity until you need it.
- Install smartphone antivirus software, such as F-Secure Mobile Anti-Virus ($35 a year; f-secure.com).
- Finally, read your phone’s user manual to learn about its unique security features, and use them.
Eugene Kaspersky is head of virus research at Kaspersky Lab (kaspersky.com), an anti-virus software company.
6. How can I make a personalized email address?

Snagging an address like chunkylover53@aol.com was cool back when email was still a novelty, but nowadays you might want something more professional. For an email address that uses your name (or anything else you want), you first have to own the domain name (.com). There are dozens of registrars online that you can use to buy a domain; one of the best values is GoDaddy.com, which offers free email hosting as part of its $9 annual fee.
Once your domain is active, log on to GoDaddy and choose the account management option to activate email hosting and to set up your new address. The easiest thing to do is create a “catchall” address so that any messages people sent to “@yourdomain.com” would be automatically forwarded to your existing Gmail or Yahoo account. (You can even set those accounts to send messages that appear to be from your new personalized address.) This allows you to give out different email addresses for different situations. For example, tell only friends about the “john@” address, and use a “junk@” address when you need to register at a website. Then set up filters to file messages accordingly. You can even reuse chunkylover53 if you like—after all, it’s your domain now.
Merlin Mann is the editor of the productivity-tips blog 43folders.com.
7. How can I surf the web anonymously?

You don’t have to be a conspiracy theorist or a criminal to be uncomfortable with the fact that your online movements are frequently tracked and recorded. Maybe you don’t want commercial websites using your browsing habits to inform their marketing, or perhaps you want to post an opinion to an online forum without worrying that it could be traced back to you. Most tools that help you surf anonymously do it by rerouting the data coming out of your computer, called traffic, so that it appears to be coming from somewhere else.
Anonymous Surfing ($30; anonymizer.com) does this by shuttling all your traffic through its own servers. A free tool called Tor (tor.eff.org) uses a network of hundreds of servers, called nodes, and reroutes your traffic through several of them. To the sites you visit it will appear that you’re coming from the last node in the circuit. This also protects your traffic in transit. If an online snoop is watching your data, all he’ll see is that you’re moving between two nodes. He won’t know where you’re coming from or where you’re going. Tor will slightly slow your browsing, and both services will prevent sites such as Amazon and Yahoo from remembering who you are and keeping you signed in each time you return—but then again, that’s the point of anonymity, isn’t it?
Annalee Newitz is a tech writer and former policy analyst with the Electronic Frontier Foundation, a nonprofit think tank dedicated to technology issues.
8. How can I guard against spyware?

If your Windows computer runs unusually slowly, shows extra pop-ups, or crashes often, it might be infected with spyware—programs that commandeer your machine to collect information for advertising, market research or outright theft. Think spyware is old news? A recent study shows that 89 percent of consumer PCs are infected, the highest level since 2004 (Macs are mostly immune). Normally, you can clean your computer with programs like Microsoft Windows Defender (free; microsoft.com), but it’s easier to avoid getting infected at all.
Before installing a program (especially screensavers, toolbars and peer-to-peer programs such as KaZaA), try to discern how the company behind it earns money. It could be profiting by quietly bundling spyware. Ironically, some of the sites you should be most wary of are ones with logos promising they’re safe. Plenty of good sites have these seals too, but don’t rely on badges to protect you from scammers. Also, do a search to see if others have had problems with the product. If it fails any of these tests, skip it—you´ll be glad you did.
Ben Edelman is a doctoral student at Harvard University, where he researches spyware, internet advertising, and online fraud.
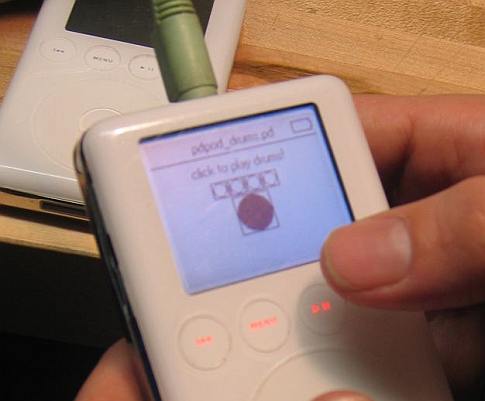
9. Can I use my own songs as ringtones?

There are a couple ways to swap that horrible default chirping noise for something more pleasant without shelling out $3 a tone to your carrier. The easiest way is to use the web service Mobile 17 (mobile17.smashsworld.com). Sign up for a free account, enter your phone model and provider, and upload your MP3 or M4A file. Choose the point in the song at which you want the ring to start and how long a clip you’d like. In a few minutes, Mobile 17 will send a file in the proper format to your phone by email or text message (you can then save the attachment as a ringtone).
If you crave more control, clip and convert a song yourself using free sound-editing software such as Audacity (audacity.sourceforge.net), and move it to the phone by data cable, Bluetooth or email. Check your phone’s user guide to make sure it supports custom ringtones. If not, consult the phone-hacking site HowardForums (howardforums.com) to see if others have found an unofficial workaround; they usually have.
A word of caution: There’s debate over whether using a copyrighted song—even one you own—as your ringtone is fair use (and therefore legal). But there’s been no definitive court ruling either way, so let Britney ring at your own discretion.
Gina Trapani is editor of the blog lifehacker.com. Her ringtone is from the Jackson Five.
10. What music format is best?

Unless you’re an audiophile with $500 headphones plugged into your iPod, you probably won’t hear a lick of difference among the alphabet soup of formats. Even when listening on your home stereo system, the more important choice is between lossy versus lossless compression. Lossless compression preserves all of a song’s audio information, so the compressed file sounds just like the original—and stays fairly large, around 10MB per minute.
Windows Media Player, iTunes, and RealPlayer all give you the option of ripping CDs to a lossless format, such as WMA; FLAC and Monkey’s Audio (APE) are common open-source lossless formats. Lossy compression creates much smaller files (about 1MB per minute) by removing the parts of the sound you’re least likely to miss. MP3 is the most widely supported lossy format, but newer codecs such as AAC and Ogg Vorbis provide better sound than MP3 at similar file sizes.
Note that you can’t go from lossy back to lossless—those crystalline highs and gut-shaking lows are gone forever. Most online music stores lock you into one lossy format that has copy protection encoded into it, limiting the number of computers or type of portable player or software the song will play on—potentially annoying in 5 or 10 years when your equipment changes and your entire Def Leppard collection is suddenly worthless. The best way to future-proof: Own, don’t rent. Buy used CDs on Amazon or eBay and rip them to a lossless format. Alternatively, rip to MP3 at a high bit rate (320 kbps), and store those discs in your Mom’s attic.
Jonathan Coulton is PopSci´s podcaster and contributing troubadour, as well as a professional musician and software engineer. Give him a listen at jonathancoulton.com and popsci.com/podcast.
11. Why do batteries explode?

Earlier this winter my Solitude Noise Canceling headset did something ironic: It emitted a piercing pop. When I opened the battery cover, I found a disfigured AAA Duracell seeping gray foam. So I sent the battery and headset to Duracell to find out what happened. Apparently, it didn’t explode; it “vented.”
All batteries sold in the US contain plastic safety vents designed to release any uncommon buildup of hydrogen gas, a by-product of the chemical reaction that generates electrical charge inside the battery. A scientist at Duracell says that batteries rarely explode but that when they do, it’s usually because they lack these vents and are probably counterfeit. (Knockoffs also drain more quickly, so don’t buy your batteries from shady sources.) But the battery I used was genuine. So what caused the hydrogen buildup? Apparently, forgetfulness—I’d left the headset on, discharging the battery beyond Duracell’s recommended low-voltage threshold of 0.7 volt. As an alkaline battery drains, it becomes less alkaline, creating excess hydrogen gas until the pressure triggers the safety vent. The result is a loud release of gray battery ooze: caustic potassium hydroxide.
Nicole Dyer is the headlines editor at Popular Science. This is her first battery incident.
12. Is the music industry still suing people?

You bet. Since September 2003, the major record companies, including EMI and Warner Bros., have been suing adults and children alike for sharing music through software like KaZaA, Morpheus, and LimeWire. The industry recently stopped disclosing national figures, but as of last spring it had announced lawsuits against more than 18,000 people, and representatives confirm that the legal campaign continues.
What happens to those who are sued? The record companies generally offer to settle for around $5,000, so most cases never make it to court. So far, the lawsuits have targeted only people uploading files (that is, making files available to other users), although many file-sharing programs do this by default. To stay off the industry’s radar, disable sharing in your program or just remove offending files—anything copyrighted—from “shared” folders. Be extra careful with BitTorrent software, which automatically uploads files as they’re downloaded. If you do get a notice, consult an attorney who specializes in copyright law as soon as you can to discuss your legal options.
A: Fred von Lohmann is a senior staff attorney with the Electronic Frontier Foundation, a nonprofit cyber-liberties organization based in San Francisco.
13. Can I wipe my name off the web?

Not really. There are so many aspects of your life that leave your name scattered around the web, it would be a full-time job trying to track down every mention. But you can get back some anonymity. Start by entering your full name and any nicknames into major search engines (like Google and Technorati) and photo sites (like Flickr). Then group the results into two categories: sites where you supplied your name, photo or data, and those where you didn’t. For either, try to contact the owner of the site or the person responsible for its content and ask them to take it down. When it’s a document or photo you created that’s somehow migrated out of your control, try citing copyright law, which prevents others from posting your content without your permission. Many sites list a procedure for removing this type of material. One way to keep a low profile from the start is to use a free tool like fakenamegenerator.com, which creates generic usernames, passwords and other information you can use to register on web sites.
Lauren Gelman is the associate director of Stanford Law School’s Center for Internet and Society.
14. How can I tame my overflowing inbox?

Start by checking your email less often—say, once an hour—and by always processing, but not necessarily responding to, new mail right away. Focus on taking action on your emails, rather than just rereading or filing. Quickly scan your messages for appointments, anything you might need to reference again, and requested actions, and immediately make notes in your calendar and to-do list.
For emails requiring only a quick response, send your reply as soon as the message arrives, and keep it short. If the recipients need more information, they’ll tell you; just move it off your plate. If you get many similar requests, use an application like QuickTemplates for Windows ($24; mapilab.com) or MailTemplate for Mac ($15; mactank.com) to knock out boilerplate responses. Finally, simplify your email filing system as much as you can stand. Put anything requiring a near-term reply in a folder labeled “To Respond” and the rest in one called “Archive.” Rely on your program’s search tool to find what you need. To move messages fast, set up keyboard commands with apps like SpeedFiler ($20; claritude.com) for Windows or, for Mac, Mail Act-On (free; indev.ca).
Merlin Mann is the creator of the productivity-tips site 43folders.com.