Today, the Washington Post (newly owned by Amazon’s Jeff Bezos) posted a brief note admitting that certain pages on the Post’s website had been hacked by the Syrian Electronic Army. The Syrian Electronic Army, a group of hackers known for infiltrating and hacking western news organizations that have criticized the Syrian government, is not exactly organization to shy from gloating, and tweeted its victory, saying it had also hacked the websites of Time and CNN, “in one strike.” They did it by hacking a service called Outbrain that most readers haven’t heard of, but that most publishers have. In fact, it’s one that we use here on PopSci, though we have not, as yet, been hacked. We’ve been told by two sources at Outbrain that the hack was carried out by phishing an Outbrain employee via email–a standard Syrian Electronic Army tactic.
Outbrain is responsible for the “related stories” links you see underneath lots of posts on publications all over the internet. Outbrain is one of many services that help publications make money in a time when lots of publications aren’t really making any money. Those related stories links are in two columns: internal and external. The internal links are links to stories by your own publication (or in-network publications; PopSci might include a link to our photography sister site, PopPhoto). The external links are from brands or publications; they’re ads, basically. If Nike wants to link PopSci readers to a cool new shoe’s site, or a new publication wants to make PopSci readers aware of their site, it can pay Outbrain to stick a link into that external links section. Then, as a reward for allowing those links on our site, Outbrain pays us a portion of that. How large that portion is depends on the individual deals struck with Outbrain, but I can say that PopSci‘s deal gives us 60 percent of the cash paid by Nike, or whoever, to Outbrain. An Outbrain representative tells me that’s a pretty standard split.
Outbrain is very popular; it’s easy and unobtrusive and gives lots of money to publishers. We use it, as do the Guardian, USA Today, the Daily Beast, Slate, CNN, Mashable, and Fast Company, among others. It’s not something readers really notice, but Outbrain has complete control over that block of links.
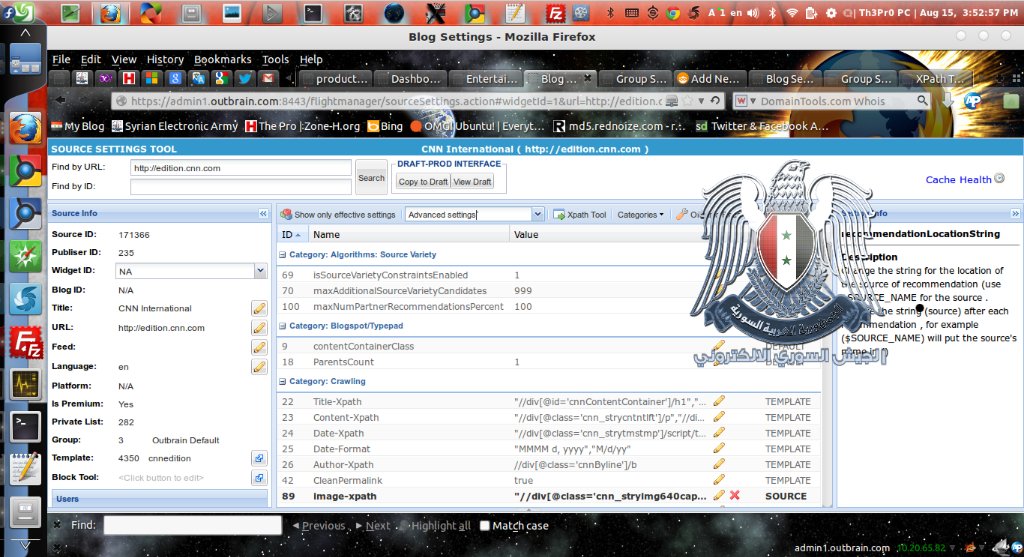
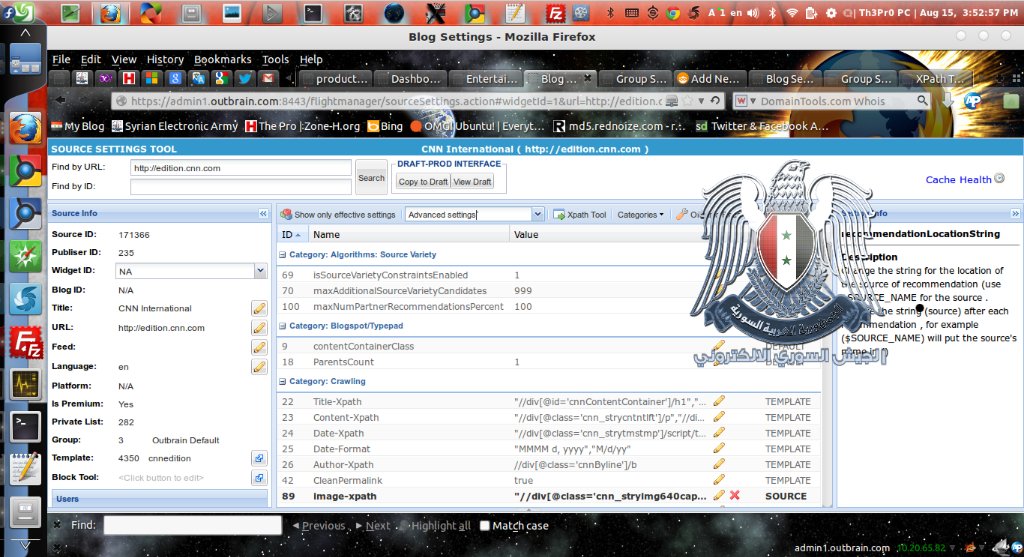
So if someone could get access to Outbrain, they’d have a nice little backdoor into all sorts of other publications, which is exactly what makes it such a sneaky and clever avenue for the Syrian Electronic Army to take. Diana Fox, the director of business development at Outbrain, told me that the hack was done by phishing, which is a standard Syrian Electronic Army tactic–they try to trick people into entering their usernames and passwords. “It wasn’t like they hacked into our back end,” she says. “They literally had one person fill out information [like] their email address and got into our stuff that way.” Lisa LaCour, on the marketing side of Outbrain, confirmed that this was the method used by the SEA to get access through Outbrain.
Phishing is a low-rent tactic, but it’s astonishingly effective; it’s the method the SEA used to hack into SocialFlow, the New York Post, and other companies earlier this week. It also explains how the SEA “compromised emails of Outbrain,” as one hacker told eHackingNews today.
