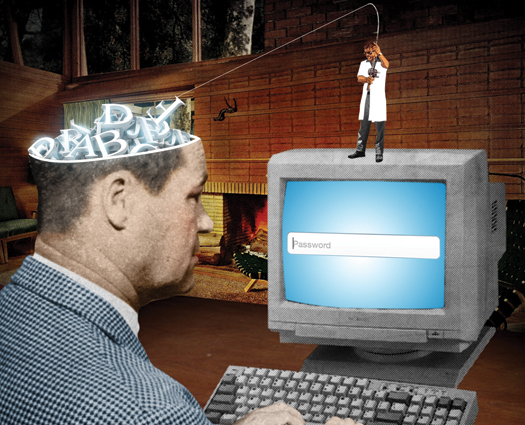
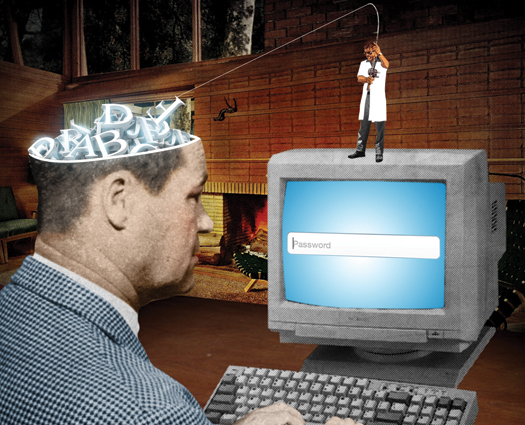
Hristo Bojinov wants you to forget your password. More precisely, he wants you to never really know it in the first place. Bojinov, a computer scientist at Stanford, and his colleagues have developed a computer program that can implant passwords in a person’s subconscious mind–and retrieve them subconsciously too. The technique could make it impossible for, say, a high-security government agent to reveal his password; the agent wouldn’t actually know the secret code. Eventually, the use of subconscious passwords could even trickle down to the rest of us. And considering the precarious state of password protection, that probably can’t happen soon enough.
“The problem with passwords is that they are easy to breach,” says Ram Pemmaraju, the CTO of security company StrikeForce Technologies. The tools for cracking them, such as malware, are easy to come by. New processors and open-source software can break an encrypted password in days, if not hours or minutes. Take a seven-character password with upper- and lowercase letters, numbers, and symbols. Five to 10 years ago, the average computer would have needed more than 1,000 years to guess it. Today’s home computers can do it in about a month. Because of this increasing computer power, some experts recommend 20- to 30-character passwords. But human laziness is also a huge problem. Who wants to remember a 30-character password? One recent study found that 5 percent of passwords are some variation of “password.”

If a person could subconsciously learn a password, though, he would never have to bother memorizing it. He wouldn’t forget it by accident. And he’d never write it down on a Post-it note for others to find. Those are the benefits Bojinov had in mind this summer at the prestigious USENIX Security Symposium, where he presented his study–the first to show that people can subconsciously store passwords and retrieve them from their minds. In the experiment, participants learned a password by playing a computer game. On the screen, black circles fell one after another from the top to the bottom of six columns labeled S, D, F, J, K, and L. When a circle reached the bottom, the player typed the letter corresponding to that column. The game, which is nearly 4,000 keystrokes long, took about 30 to 45 minutes to complete. The players didn’t know it, but the game contained a password–a sequence of 30 letters that they typed in 105 times. By the time players finished the game, they knew the password well enough that it seemed slightly familiar, but they still couldn’t recognize it, let alone recite it. (On average, they rated the password’s familiarity as a 6 out of 10, and a random password as a 5 out of 10.)
Five percent of passwords are some variation of “password.”To use the password, the participants played a 5- to 10-minute version of the game. This time, the software compared how accurately they typed the actual password versus randomly generated 30-letter sequences. Seventy-one percent of participants scored better on the real passwords than the fake ones. Playing the game two weeks later, 61 percent did.
In the future, people could use a similar game to log into their computers in the morning. But Bojinov cautions that the work is still preliminary. The learning process takes too long for the majority of people, he says, so he’s currently focused on honing the technique for high-security situations–the kinds of applications in which a 45-minute password ritual would be worth the trouble. He suggests that the system could be used as a form of secondary authentication, a substitute for the security questions now required to reset a password on an e-mail account. No matter what the application, Bojinov says researchers still need to answer critical questions about the technique. How can they make it work for more people? What’s the best way to speed up the process? And how long do subconscious passwords last?
The answers to those questions could lead to an interesting twist in password protection. Russell Dietz, CTO of data protection company SafeNet, says the current strategy is to secure a system against both human cleverness and human failure. “You want to prove that someone is who they are while eliminating the weak link—the human users themselves,” he says. But as Bojinov’s research demonstrates, human experience might be the thing that no other person, or computer, can fake.
