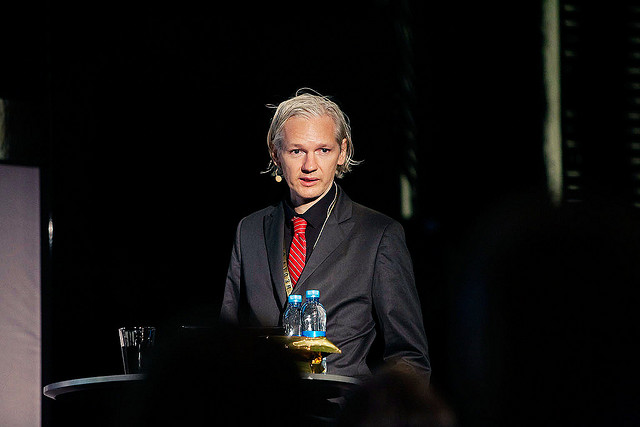
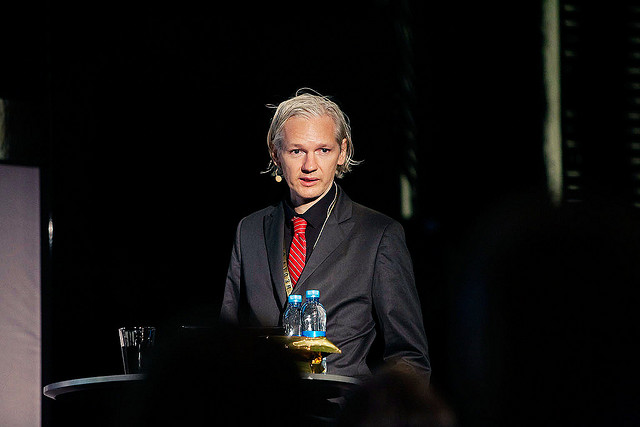
Once your leader has been compared to a Bond villain, you might as well go all the way, right? A few months back, Wikileaks released a giant file that’s been referred to as the “thermonuclear” option, should the organization’s existence be threatened: A huge compendium of some of the most damaging secrets Wikileaks has collected, protected with an intense brand of secure encryption–for use as insurance. With Assange now in police custody on sex crimes charges, the “poison pill” is on everyone’s mind.
The pill in question is a 1.4GB file, circulated by BitTorrent. It’s been downloaded tens of thousands of times, no mean feat for what, at the moment, is a giant file with absolutely no use whatsoever. It’s waiting on the hard drives of curious Torrenters, Wikileaks supporters, and (you can bet) government agents worldwide, awaiting the password that’ll open the file to all. Although no one is sure of its contents, the file is speculated to contain the full, un-redacted documents collected by the organization to date (including, some are guessing, new documents on Guantanamo Bay or regarding the financial crisis). It has yet to be cracked, at least not publicly, though there is a hefty amount of activity from those trying, at least a little, to break into it before Assange releases the key.
What makes this so pressing is Assange’s recent arrest in London, on, to say the least, somewhat controversial sex crimes charges in Sweden. There’s been speculation that this could be the lead-up to more severe prosecution–certain American politicians have called for prosecuting Assange for “treason,” apparently not realizing or caring that Assange is an Australian national–and could in turn lead to his releasing of the password for these documents.
The file is titled “insurance.aes256,” implying that it’s protected with an AES 256-bit key, one of the strongest in the world. The thing is, there’s no actual way to figure out the type of encryption used. Though there’s no particular reason for Assange to lie about the security he used, it’s something to keep in mind. Let’s assume for the moment that it is indeed an AES-256 encryption, which begs the question: What is AES?
Advanced Encryption Standard
Advanced Encryption Standard, or AES, is a cipher standard which came into wide use in 2001. AES is a block cipher rather than a stream cipher, meaning “blocks” of data are converted into encrypted gibberish, 128 bits at a time. It’s perhaps the most-used block cipher in the world, used by, for example, the Wi-Fi protection known as WPA2. But it came to prominence in 2001 as a result of winning a contest held by the National Institute of Standards and Technology to find a new standard encryption. That led to its adoption by the NSA. That’s right, Assange’s “poison pill” is secured by the U.S. government’s own standard.
Though AES is an open and public cipher, it’s the first to be approved by the NSA for “Top Secret” information, the term used for the most dangerous classified information. It is, in short, a tremendously badass form of protection.
An AES encryption doesn’t work like, say, a login. The keys are just strings of binary (in the case of AES-256, 256 binary symbols) rather than words or characters, and entering the wrong key won’t simply disallow access–it’ll produce elaborately encoded gibberish.
There are three variants of AES, which differ in the size of their keys (128, 192, or 256 bits), though they all use the same 128-bit block size. The size of the key has other implications within the algorithm itself (and slightly increases the encoding time), but mostly, it increases the amount of time needed to break it with what’s called a “brute force attack” (more on that in a bit). The three variants also carry different numbers of “rounds” protecting their keys. Each round is sort of like a layer of further obscurity, making the original data all the more disguised. AES-128 has ten rounds, AES-192 has twelve, and AES-256 has fourteen.
Those rounds make it effectively impossible to compare the ciphered data with its key and divine any sort of pattern, since the data has been so thoroughly mangled by, in this case, 14 rounds of highly sophisticated manipulation that it’s unrecognizable. The rounds make an already secure algorithm that much more secure.
Possible Attacks
There are a few different ways of cracking a code like this. Many rely on some other information besides the code given. Side-channel attacks, for example, require an observation of the actual decoding: This might include data like the timing of deciphering, the power it takes to run the computer doing the deciphering, or even the noise a computer makes while deciphering. There are measures you can take to spoof this kind of thing, but even if Assange hasn’t, side-channel attacks won’t work in this case.
Another kind of attack, the one that’s come closest, is the related-key attack. This method requires multiple keys, somehow related, working on the same cipher. Cryptographers have actually had some very limited success with related-key attacks, managing to greatly reduce the amount of possible correct passwords–but there are huge caveats to that. Related-key attacks require an advanced knowledge of the cipher and key that cryptographers never really have in the real world, like, say, a ciphered text and a deciphered text. Most modern key generation tools, like TrueCrypt and WPA2, have built-in protections against related-key attacks. And, worst of all, that success, which broke a 256-bit code, required a handicap: an altered encryption with less rounds. A related-key attack won’t work on Assange’s jacket-full-of-dynamite.
The time it takes to crack a code is thought of in terms of how many possible correct passwords there could be. If you’re looking at a 256-bit password with no knowledge of anything, trying to just enter every conceivable combination of 0s and 1s, you’d have a “time” of 2256. Nobody measures the time it would take to crack one of these codes in hours, months, years, or centuries–it’s too big for all of that, so they just use combinations. Trying to crack all of those combinations manually is called, aptly, a brute force attack, and in a 256-bit instance like this one, it’d take, roughly, a bajillion years to succeed (that being the scientific estimation). Even with all the supercomputers in the world working in concert, with a flawless algorithm for trying the different combinations, it would take hundreds of thousands of years. Your average dude with an Alienware? Forget about it.
In the case of the successfully cracked 256-bit code above, the cryptographers only managed to narrow it down to 270 possibilities–and they only got through the 11th round. Besides, 270 combinations is, in real world terms, not really much closer to cracked than 2256. It’s still dramatically unfeasible.
The best possible method of cracking the code might be the simplest: Beat it out of him. This is, I swear to God, a real technique, called rubber-hose cryptanalysis. Assange is already in custody–the most efficient way to get his password is, by far, torture. It’s also authentic in that it’s the only type of cracking you’d actually see in a Bond movie. Sure as hell better than waiting several million years for a brute-force attack, right?
Conspiracies Are Afoot!
That brings us to the conspiracy theory section, perhaps the most fun section of all. Encryption, especially the corners of the Internet in which it is feverishly discussed on near-incomprehensible message boards, is a topic that naturally invites conspiracy theories. One of the most interesting, regarding AES, is the “secret door” theory, speculating that one of the reasons the U.S. government selected the AES algorithm over several other worthy algorithms is that the government has the ability to crack it. In that case, the government has already cracked Assange’s poison pill and knows exactly what it is–and regardless of what it is, it’s almost certainly in the government’s best interest to keep it quiet.
It’s a great conspiracy theory because it makes sense in terms of motivation, and it’s something that would be impossible to prove decisively either way. In this case, however, it seems unlikely. The government’s cryptographers are phenomenally talented, but they aren’t necessarily more talented than those outside the government who for whatever reason have been working on cracking AES since its creation. The secret door isn’t impossible, but it’s extremely doubtful.
