What Spying Looked Like In The 1960s
Life magazine's cover story from 1966 gives us a glimpse of what privacy invasion used to mean.
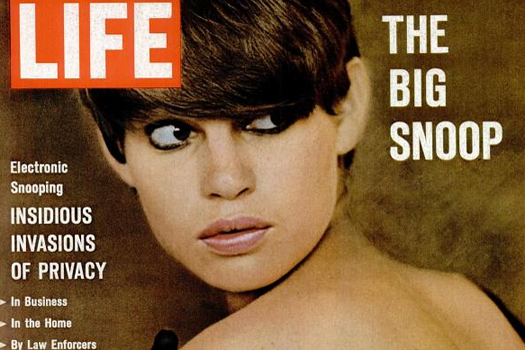

Covering Snoops
With all the depressing, worrisome news floating around this summer about the NSA, spying and metadata, sometimes it’s good to take a break and indulge some nostalgia for the good old days, when spying seemed a little bit…sexier. A little more Bond-y, if you will.
Except that, even in 1966, the government had “been electronically spying on its citizens for years,” as the author of this 1966 LIFE Magazine cover story writes. Except LIFE was talking about putting a bug in the olive of your martini, not cataloging every single phone conversation you’ve ever had.
The author goes on: “Despite the protections against invasion of privacy afforded by the Fourth Amendment of the Constitution, bugging is so shockingly widespread and so increasingly insidious that no one can be certain any longer that his home is his castle–free of intrusion.” Sound familiar, Edward Snowden?
Though the fact that we all carry cell phones everywhere we go makes it even easier to listen in on someone nowadays, snooping was a novel, rapidly expanding trade in the ’60s, as technology allowed smaller and smaller eavesdropping devices (sugar cube sized! LIFE gushed). Microphones in wristwatches and cuff-links, hidden transmitters in pens and innocuous-looking paintings of fruit–some labs were even experimenting with putting body-heat-powered FM transmitters in animals.
See more Bondtastic gadgets in the spreads below. Click the image captions to see the pictures in full screen mode–with a little squinting you can read most of the text.

Invasion Of Privacy

The Eavesdropping Trade

Divorce Spy!

Ace Bugging
All Ears