You are more than a data point. The Opt Out is here to help you take your privacy back.
YOUR PASSWORDS are probably terrible and you need to make them stronger. Yes, we know there are few things more annoying than brainstorming a fresh credential every time you need to do the tiniest task, but they’re one of the most practical ways to keep hackers and other malicious actors out of your business.
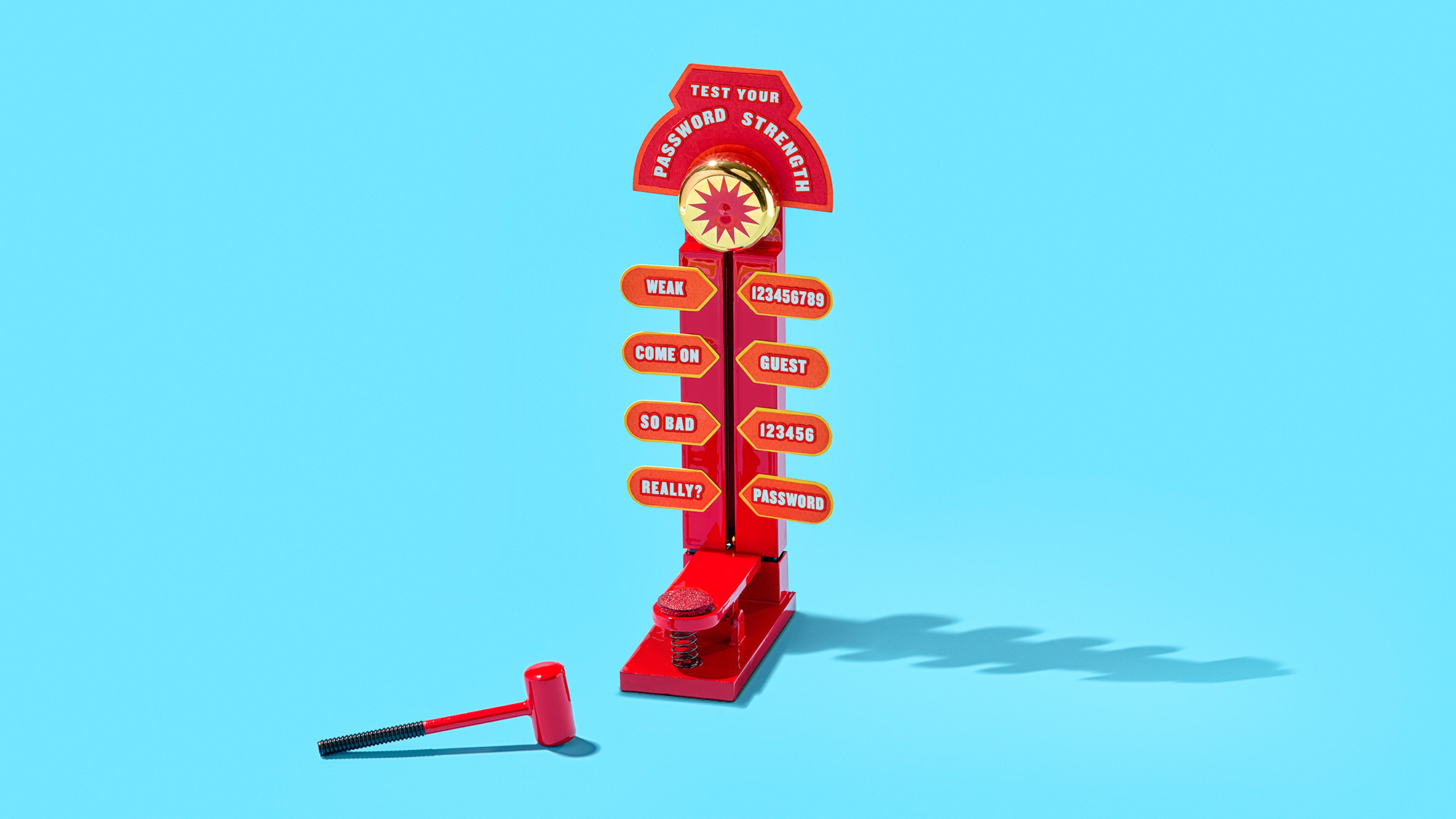
Tech companies, journalists, and organizations concerned with cybersecurity awareness have spent years underscoring the importance of secure passwords. Sadly, it seems there has been little payoff. A 2022 report by credential manager NordPass is truly embarrassing, listing “password,” “123456,” and “123456789” as the three most common passwords. It doesn’t get much better than that as you go further down, either: “Password1” ranks at No. 192.
It’s worth noting that the tech industry has spent decades imagining a password-free world, and some companies are already offering options to circumvent or ditch this type of authentication altogether. But as long as passwords remain the primary way to access our data, we’ll need to up our game to properly protect our information and money.
What is a strong password, and why is it so hard to create one?
In their attempts to gain access to your accounts, malicious third parties might try to use methods like guessing attacks. There are several variations to this approach, but they all work in a similar way: grabbing a key (a known common password or a personal credential leaked online) and seeing how many doors it will open.
[Related: Why government agencies keep getting hacked]
Of course, attackers aim for efficiency, so they’re not manually typing on a laptop somewhere. They’re using software to automatically try every entry in a common password dictionary, for example, or using information from known data breaches to try leaked passwords and/or their potential iterations. This is because people don’t update their passwords as regularly as they should (they do it once or twice a year instead of the recommended every three months), and when they do, they tend to make only minor changes to the ones they already have.
This is why strong passwords are unique, long, and peppered with special characters like punctuation marks, numbers, and uppercase letters. When we say unique, we mean words you can’t find in the dictionary. Common or famous names are out too—the more original the password, the better. The length of a password and the use of special characters both increase the odds that it is truly unique. It’s just math—the greater the number and variety of characters you use in your credentials, the more possible combinations there are, and the harder they will be to guess.
A lot of people come up with their own secret code to develop passwords using easy-to-remember phrases from songs, poems, and movies. A classic approach is to replace letters with numbers (like 4s for A’s and 0s for O’s) and alternate uppercase and lowercase letters. If this is what you do, you’re on the right track, but you actually need to make your personal cryptography even more complicated to truly add security to your passwords. We won’t tell you how we encrypt our credentials, but you can create your own written language or alphabet by replacing letters with other characters. Just keep in mind that Klingon was built from utter gibberish, so the sky is the limit.
Naturally, the cost of added difficulty is a higher cognitive burden. This means that the further a password is from a word or phrase you commonly use, the harder it’ll be for you to remember. That’s complicated as it is, but if you consider that the average person has around 100 online accounts, the feasibility of remembering all of those encoded unique passwords goes violently out the window.
Help us help you
Password managers. That’s it, you think, that’s the solution. Theoretically, it is. These stand-alone apps, downloadable extensions, and built-in browser utilities have three main abilities: suggesting strong passwords, storing them securely, and remembering them whenever you visit a website where you have an account.
Basically, these tools allow us to outsource the whole credentials problem out of our lives, on the condition that we remember one good master password—or hold another type of authentication key, such as a fingerprint. And it works. Depending on the password manager you get, you’ll find features like good design, syncing across devices, and the ability to choose when fields autofill.
But password managers are not perfect, and what makes them convenient also makes them incredibly attractive targets for hackers. After all, the proverbial basket that holds all your cybersecurity eggs is a great deal: Creeps can crack one account and take all your credentials for free. Companies like NordPass, KeyPass, 1Password, and others have taken extra precautions to secure their apps, incorporating features like constant logouts and unique single-use codes in case you lose access to your account.
[Related: How to get started using a password manager]
Still, sometimes these measures are not enough. In December 2022, LastPass, another popular password manager, reported a security breach that included users’ names, phone numbers, emails, and billing information. As if this weren’t concerning enough, the company’s crisis management at the time was lacking, and it only disclosed details about the breach and what steps should customers follow in a blog post published more than two months later.
Beyond breaches, some features in password managers are generally less than secure. In a 2020 review, researchers from the User Lab at the University of Tennessee, Knoxville, mentioned autofill as one of the most concerning. This is especially true when password managers automatically enter credentials without any input from the user. In cross-site scripting (XSS) attacks, hackers inject malicious scripts into a website’s code to steal a password as soon as the right fields are populated. “If a password manager autofills passwords without first prompting the user, then the user’s password will be surreptitiously stolen simply by visiting the compromised website,” explain study authors Sean Oesch and Scott Ruoti.
The likelihood of a successful XSS attack varies depending on factors like whether the site is using a secure connection (HTTPS, for example). But it’s always best to opt for a password manager that either requires user interaction for autofill or allows you to manually disable the feature. Most browser-based password managers don’t require user interaction before filling in credentials, but there are some exceptions. Mozilla Firefox automatically populates fields by default, but you can turn this feature off by clicking the main menu (three lines), going to Settings, Privacy & Security, and scrolling down to Logins and Passwords. Once you’re there, uncheck the box next to Autofill logins and passwords. An even easier solution is to use Apple’s Safari, which always requires user input for autofill. If you’re on a PC or don’t want to switch browsers, the study found the browser extension of the popular 1Password app will also require a click before it reveals your information.
Drink water, wear sunscreen, and enable multifactor authentication
Healthy habits lead to better lives, and when it comes to your life online, using multifactor authentication is truly self-care.
This now practically ubiquitous feature is an extra layer of security that prevents virtual sneaks from accessing your accounts even when they have the right credentials. This means that even if your passwords leak all over the internet, people won’t be able to use them if they don’t have an extra form of verification like a text sent directly to your phone, an app-generated code, a prompt on another device, or a biometric element such as your fingerprint or face.
Which and how many of these you use will depend on the level of security you want your account to have and what is most practical for you. Keep in mind that the more methods you enable, the more ways there will be to access your account. That’s not exceptionally secure, but it might make sense if you, say, regularly lose your phone or get locked out of your accounts.
[Related: How to keep using two-factor authentication on Twitter for free]
Just know that even though most modern platforms offer some kind of multifactor authentication, you won’t find every type every time. The most common option is authentication via a code sent over SMS text, followed closely by authentication via a code-generating apps. These are essentially the same, but the latter method uses the internet instead of phone networks to deliver the code. It’s worth noting that text messages traveling through the electromagnetic spectrum can be intercepted, and according to Ruoti, the low standards US telecom companies use when authenticating users make it possible to port someone’s phone number to a SIM card and receive their authentication codes on your device. If this concerns you, you can opt for more sophisticated alternatives, like security keys. These work exactly like your home keys—just plug them into your gadget’s USB port when prompted, and you’re done. We have an entire guide solely dedicated to helping you choose the best multifactor authentication method for you, if you want to do a deep dive into your options.
But even if some approaches are better than others, one thing will always be true: Any multifactor authentication is better than none at all. So if you have a phone, it’s an excellent idea to set up SMS codes for whenever a new device tries to access your account. Just make sure to disable the ability to preview message content on your lock screen, or somebody could use your codes by just stealing your phone. On Android, you can do this by going to Settings, Notifications, and turning off Sensitive notifications under Privacy. On iOS, open Settings, go to Notifications, tap Show Previews, and choose Never. If you want to see previews for less sensitive notifications on your iPhone, you can turn off previews for individual apps instead. If you receive codes via the Messages app, for example, open Settings, go to Notifications, tap Messages, find Show Previews, and choose Never.
May this be the sign you were waiting for to get your act together when it comes to online security. Don’t wait until spring cleaning; don’t wait until it’s time to make New Year’s resolutions—do it now. Keep your credentials off 2023’s list of worst passwords. That’s a list you don’t want to make.
Now off you go to change those passwords. We’re glad we had this talk.