

This story has been updated. It was originally published on May 11, 2017.
You may have heard that the Biden administration warned US companies to be on alert for potential Russian cyber attacks, but even if you’re not likely to be targeted by a state actor, it’s still important to take your email security seriously—scams of all kinds have thrived during the pandemic.
Take this textbook example of phishing from 2017, targeting Google Docs users: People received emails with what looked almost exactly like a shared document, tricking them into granting access to a not-particularly-nice piece of software. From there, the attack could spread to other inboxes, as emails are an easy, low-cost way to fool people into letting their guard down.
With that in mind, we’re here to make sure your inbox is tightly buttoned up against phishing attempts, malicious attachments, and more. While we can’t guarantee your safety, these precautions will certainly minimize your risk.
Fight back against phishing
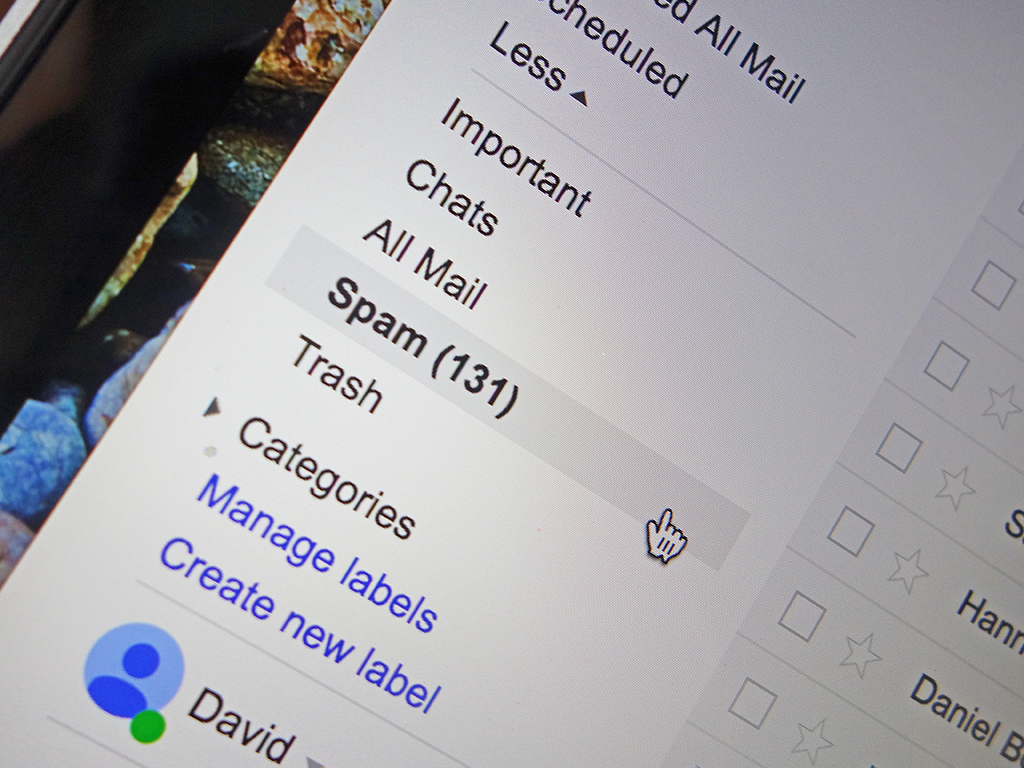
Whether you use Gmail online or a desktop program like Microsoft Outlook, your email service already comes with a decent set of security tools. For example, it can snag suspicious emails and automatically toss them into your spam folder. To help out, report spam whenever you find it, making it easier for the program to spot something untoward in the future
Be wary of any email asking you to click a link, especially if it comes out of the blue without any context—and particularly if it comes from someone you don’t know. Phishing emails can appear to come from trusted contacts, but they often arrive from bizarre-sounding email addresses. To double-check the identity of the sender, and pull up the full header information for suspicious emails. To do this in Gmail, for instance, open the drop-down menu (three vertical dots) on the right side of the message, then choose Show original.
Unfortunately, even a message that comes from a known contact with the correct email address isn’t necessarily safe. As we’ve said, if one of your friends or family members is hit by a phishing attack, their valid email address can be used to send you a dangerous message. This means that context is key. Were you expecting a message with a link in it? Does the message make sense? If you’re unsure, it’s worth a quick phone call or text message to check that the email is what it claims to be. Ask the same questions before opening any attachments: Were you expecting them? What’s the context?

Hackers are getting better with their craft, but spelling errors and awkward layouts are still tell-tale signs of emails you should steer clear of (the spelling errors are often intentionally left in to evade spam detectors). Another check you can do is to hover over any links or attachments, which might bring up a preview and alert you to potential problems before you click.
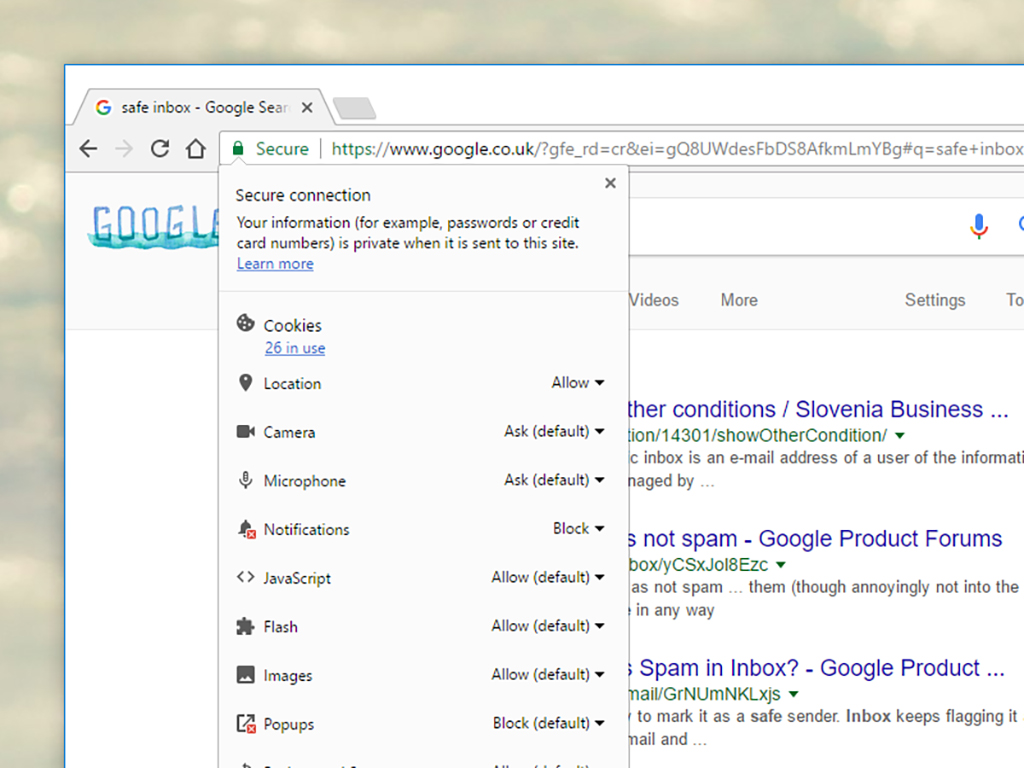
If you do click on a link, check that the URL in your browser’s address bar is the one you were expecting, and look for the green padlock symbol that shows the site is secure and trusted. If a sign-in page pops up—or if you’re in any doubt—open a new window and directly type in the URL of the site you think you should be going to, rather than following any embedded links. This will prevent you from typing your login information directly into a hacker’s hands.
Browser extensions can also help protect you from phishing attacks. Gmail Sender Icons makes it easier to identify where a message has come from, while Google’s own Password Alert warns you if you’re about to enter your Google account password into a site that isn’t made by Google. Both extensions are well worth installing if you have a Gmail account and use the Chrome browser. Not a Gmail or Chrome user? Look for add-ons that work with your own email client.
Take safety beyond your inbox
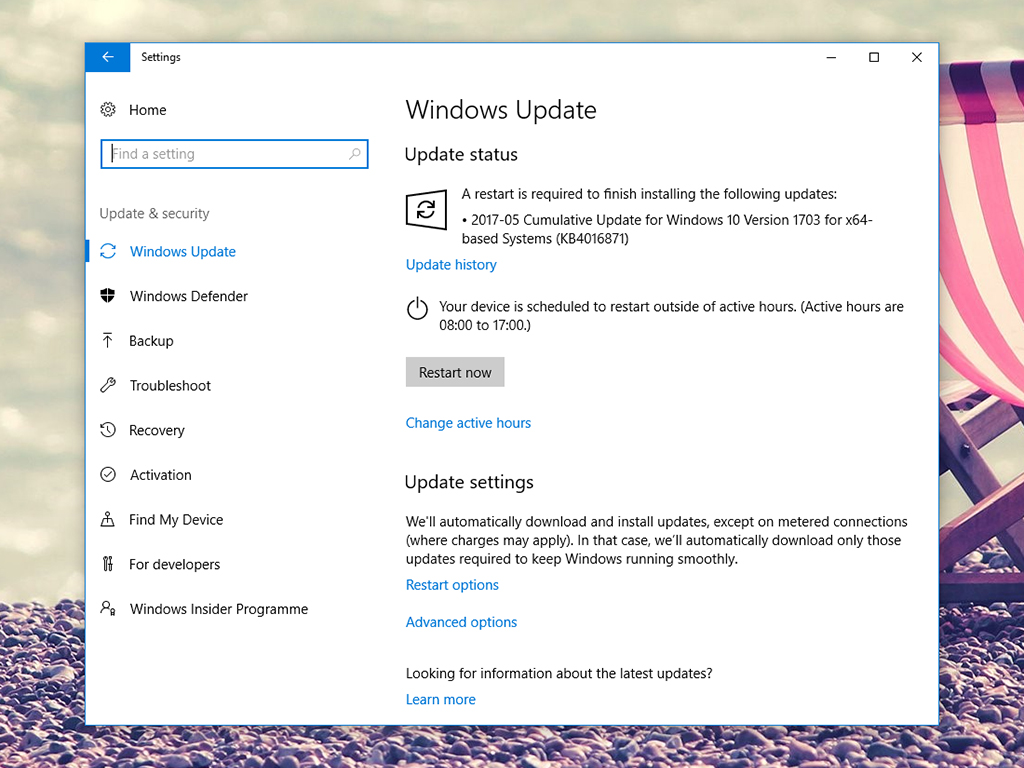
Protecting against shady links and malicious attachments goes beyond your inbox. For example, most modern-day browsers come with built-in security measures designed to thwart phishing attempts. For best results, make sure you keep your browser of choice up to date at all times (thankfully, browsers usually update automatically).
Keep your operating system and your antivirus package up to date as well. If you’re using an antivirus program on Windows, it probably features extra security measures to protect against dangerous attachments that want to do your computer harm, as well as fraudulent links that lead your browser somewhere it shouldn’t go.
You should also take precautions when using public WiFi, because unsecured networks give hackers more elbow room when it comes to spoofing sites and stealing your information. If you want to be as safe as possible when using the web away from home, we’d recommend sticking to sites that don’t deal in sensitive information and installing a VPN package to encrypt any data you do send.
Remember standard email security measures
As we’ve mentioned before, it’s a good idea to regularly check the plug-ins and add-ons connected to your email inbox. This will reveal any third-party programs that have access to your Gmail, Yahoo, or Outlook account. This is actually the recommended clean-up method for the Google Docs phishing attack we referred to at the start of this article—removing the app’s permissions means it will no longer have control of your inbox.
The place to find these add-on tools varies depending on your setup. For Gmail, head to your Google account page and click the link labeled Data & privacy. After that, scroll down to the heading for Data from apps and services you use. In the Apps and services box, click Content saved from Google services to delete any Google-run services, or Third-party apps with account access to get rid of anything you don’t use regularly or simply don’t recognize. To be clear, many of these add-ons are useful and perfectly safe. But from a security point of view, it’s a good idea to keep the number of these tools to a minimum.
Finally, stay informed: Keep an eye on the tech headlines to track the new types of attack that appear on a regular basis. While Google, Microsoft, and other companies usually deal with the latest dangers quite quickly, you’re better off hearing about a dangerous scam before it hits your inbox rather than after.
