
This NASA hack story keeps getting worse and worse. We knew that NASA had been the target of a handful off attempted cyber attacks last year, but in testimony before the U.S. House Committee on Science, Space, and Technology over the last week, we’re getting the details straight from Paul Martin, NASA’s inspector general. NASA was targeted 47 times last year and 13 of those hacks were successful, at various points handing hackers “full functional control” of critical NASA networks. At one point the agency even lost the keys to the International Space Station.
NASA is a prestigious target for hackers because of its seat atop the United States’ broader technology incubation apparatus, and because of that position it is also a strategic target for foreign state actors and cybercriminals looking to steal things they can profit from. And while the agency reportedly spends about a third of its $1.5 billion IT budget on security, things aren’t looking so secure. Securing a huge bureaucracy like NASA is difficult, no doubt. But according to Martin’s testimony, as of February 2012 only one percent of NASA’s portable devices and laptops were encrypted.
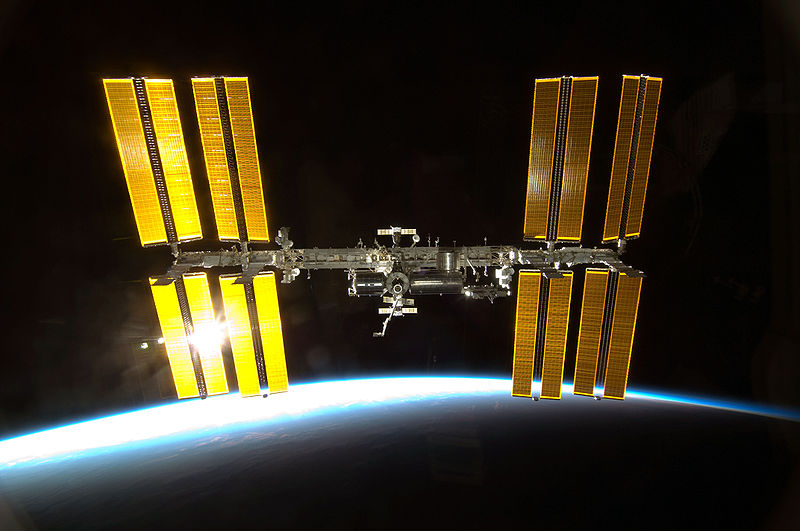
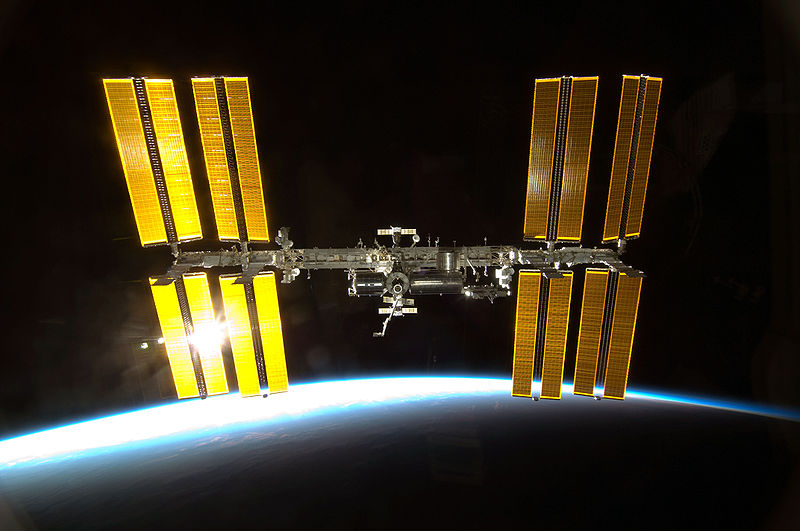
That’s exactly how the control codes for the ISS were lost. Between April of 2009 and April of 2011, 48 mobile computing devices were lost or stolen from NASA. In Mach, one of those stolen (unencrypted, of course) resulted in the loss of the very codes that command and control the ISS–the orbiting station that, should anyone need reminding, is staffed with a human crew. Other lost devices compromised data from NASA’s Constellation and Orion programs, as well as NASA employees’ personal data and Social Security numbers.
Then there are the hacks coming from outside. A particularly damning excerpt from Martin’s testimony (PDF) gives a nice broad overview of just how bad things got last year (by the way, JPL is NASA’s Jet Propulsion Laboratory, and an APT attack is an “Advanced Persistent Threat,” meaning it’s not a lone hacker or small group, but an organization with the capacity to persistently and effectively target an objective–think: foreign governments):
In FY 2011, NASA reported it was the victim of 47 APT attacks, 13 of which successfully compromised Agency computers. In one of the successful attacks, intruders stole user credentials for more than 150 NASA employees – credentials that could have been used to gain unauthorized access to NASA systems. Our ongoing investigation of another such attack at JPL involving Chinese-based Internet protocol (IP) addresses has confirmed that the intruders gained full access to key JPL systems and sensitive user accounts. With full system access the intruders could: (1) modify, copy, or delete sensitive files; (2) add, modify, or delete user accounts for mission-critical JPL systems; (3) upload hacking tools to steal user credentials and compromise other NASA systems; and (4) modify system logs to conceal their actions. In other words, the attackers had full functional control over these networks.
“In other words” — NASA has a cybersecurity problem. To its credit and to the credit of the international law enforcement community, hackers in more than half a dozen countries have been apprehended in recent months and years for NASA-related cyber crime activities. But losing the laptop with the ISS codes? Unencrypted? This doesn’t inspire confidence in the agency whose very name is supposed to be synonymous with high tech.
