‘PinDr0p’ Tech Uses Unique Noise Fingerprints to Trace Calls
Phishing scams are bad enough, but vishing – or voice phishing – is enjoying a renaissance with the emergence of...
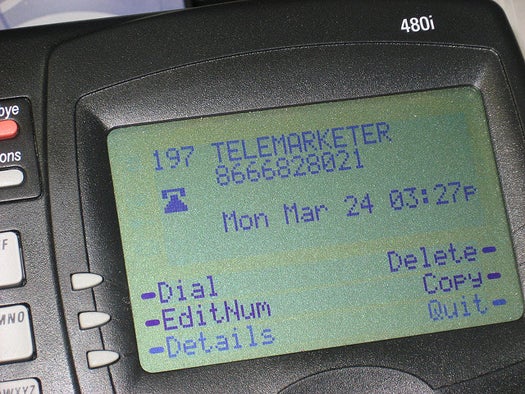
Phishing scams are bad enough, but vishing – or voice phishing – is enjoying a renaissance with the emergence of cellular and voice over IP (VoIP) networks that allow scammers to forge caller ID info and route fraudulent calls through multiple networks, making them difficult if not impossible to trace. So Georgia Tech researchers have created a novel way to identify fraudulent calls with a digital fingerprint that is unique to each individual phone as well as each individual call.
Known as “PinDr0p,” the technology can assemble an array of characteristics about a given phone call into a unique signature, determining what the team has termed “call provenance.” When a call is routed through voice networks, various artifacts are injected into the call by the networks. For instance, VoIP calls are plagued by packet-loss – tiny disruptions in audio too small for the ear to pick up – while cellular and public switched phones insert distinct background noise into calls.
Using a set of novel algorithms to analyze and assemble all these distinctive artifacts, the technology creates a multi-layered fingerprint for any given call. PinDr0p doesn’t trace a name or a precise IP address, but it can determine if the fingerprint of a phone call matches that of a phone previously used for fraudulent purposes.
In tests, the researchers analyzed calls from 16 locations all over the world. After creating a single fingerprint for a call, they were able to identify subsequent calls from that phone with 90 percent accuracy. But with each positive ID the system gets better. By the time the team had identified a call five times, the accuracy rate for subsequent calls was at 100 percent.
Given that vishing scams rely on making many hundreds of phone calls in an attempt to cast the fraudulent net as widely as possible, PinDr0p could make it a lot more difficult for scammers to misrepresent themselves over the phone. But the researchers are hard at work making the system not just a deterrent but an enforcement method; the next step for PinDr0p is using it not just to figure call provenance, but to geolocate the source of the call.