PROTECT YOUR KIDS
Cameras with behavior-tracking software will watch for danger on the playground
THE THREAT:
A kidnapper loitering in front of the local school. A thief slipping into a warehouse. A suspicious stranger dropping a bag in a hallway. The average security camera can catch all these actions, but the footage isn´t much help if the person monitoring the screens is dozing, or so wiped out after hours of viewing that he wouldn´t notice a mushroom cloud erupting on monitor three.
THE SOLUTION:
In the next five years, the security industry could be revolutionized by the spread of smart cameras that pick out shady behavior. Like a friend rousing you from a nap on the couch to check out a great play in a ballgame, these cameras will flag important events and encourage security guards-and high-school principals-to take a closer look. Instead of blankly staring at a screen for hours, says David Abrams, the CTO of Interact Public Safety Systems in Winston-Salem, North Carolina, “you´re only looking at video when the software thinks something is going on.”
As part of a test program at Hazard High School in Hazard, Kentucky, Interact has set up 16 smart cameras that can pick out suspicious parked cars, intruders climbing over the fence, or people entering buildings at odd times. The software ignores the background elements in the camera´s field of view-buildings, trees, bushes-then establishes a set of normal, baseline events and watches for unusual occurrences. Since it´s all digital, Interact´s system also enables easy Web access. The principal can view suspicious activities on a handheld wireless device, and police responding to a school shooting could tap into a live video feed of the scene from inside their squad cars.
THE ETA:
Although basic test programs are in place now, by about 2012, smart cameras should be capable of much more, says Vaidhi Nathan, CEO of San Jose”based IntelliVision. This will stem in part from the spread of higher-resolution cameras, but industry experts also expect the algorithms themselves to become more reliable and versatile. At the University of California at San Diego, computer-vision researcher Sangho Park is developing algorithms that distinguish violent from friendly behavior. Given a camera with high enough resolution, he says, his program can distinguish a friendly handshake from a punch, or a hug from a push, with 80 percent accuracy. Whether it´s behavior tracking or face recognition, though, the basic idea will remain the same. “The computer does all the work for you,” says Dilip Sarangan, an industry analyst at global consulting firm Frost & Sullivan. “It makes life a little easier for everyone.” Except the bad guys. -Gregory Mone
**PROTECT YOUR CAR **
Unmistakable identification keeps car thieves away from your ride
THE THREAT:
More than one million vehicles are stolen in the U.S. every year, with a total value of over $7.6 billion. And once thieves remove license plates and vehicle identification numbers, there´s no way of knowing who the vehicles once belonged to.
THE SOLUTION:
DataDot Technology-a startup company in Australia, which has the highest rate of vehicle theft in the developed world-has devised a way to cover valuable items in identifiers as small and invisibly scattered as hairspray droplets on a bouffant. Transparent DataDots are laser-etched with an identification number unique to you and glued to every internal surface of your car, boat or laptop. The sheer number of sand-grain-size dots on treated possessions-up to 5,000-makes it all but impossible for thieves to take them off and sell the harvested parts. In contrast, existing theft-deterrent systems such as a LoJack can be hidden in only one of about 20 places, and so can be removed much more easily.
Cops determine who stolen property belongs to by using a 50x magnifier to read the dots. If a person reporting a theft mentions that the item was Data-Dotted, police departments can access a company-run international database to find out if the car has turned up elsewhere. “The system really works in favor of the police,” says Scott McKeever, program-development director for DataDot´s American division. “They only need to locate one dot to determine an item´s owner, whereas thieves would have to remove thousands of them in order to resell a stolen item.”
Although DataDots are still largely undiscovered in the U.S., McKeever predicts that as awareness grows, they will become highly effective deterrents. In a three-year study, Australia´s National Motor Vehicle Theft Reduction Council found that cars with DataDots were 80 percent less likely to be stolen and never recovered than cars of the same make without DataDots. “Once the word spread among thieves,” McKeever says, “it was clear they wanted to stay away.”
THE ETA:
DataDot is just starting to test the consumer waters here. As part of a pilot program at auto dealerships in a dozen states, the company will apply around 1,000 dots to your new vehicle for $300-and offer you a $5,000 refund on top of regular insurance benefits if your car is stolen. The royal DataDot treatment should go nationwide this year, but in the meantime, you can obtain a DIY kit online. These kits cost about $25 and contain 500 dots that can be applied at home with a swab. Schools including San Francisco State University have started encouraging students to use them on laptops and iPods. -Elizabeth Svoboda
**PROTECT YOUR MONEY **
Flexible display technology could lead to fraud-proof bank cards
THE THREAT:
The modern pickpocket lifts a victim´s financial vitals by reading through his mail, hacking into Web sites, sucking him into complex e-mail and phone scams, or even bribing bank employees. Whatever the means, though, the results are effective: More than 60,000 people in the U.S. fell prey to credit-card fraud in 2005, at a cost of more than $1.4 billion dollars.
THE SOLUTION:
One of the reasons it´s so hard to protect yourself against modern crooks is that you´re using the same digits every time you buy something, whether it´s online or at the local diner. But that could change soon, thanks to electronic credit-card displays that will generate new account numbers on command. This way, a crook who tries to use your digits from a previous purchase will be left with an expired card.
Your card will still have a static account number. But during each transaction, you´ll also press a small button in the card. This action will instruct a microchip to spit out a new string of additional electronic digits in the small, calculator-like flexible screen. These aren´t random: Each card will start with a base number-or “seed”-and with every press of the button, an algorithm will calculate the new digits from the last one. Your bank or credit-card company will be able to verify the info because it knows both the seed and the algorithm. When it does match them up, this proves that you have the physical card in your possession and haven´t just “phished” its vitals off the Web. To thwart old-fashioned pickpockets, you´ll probably enter a static PIN as well. That way, says Dennis Brestovansky of Aveso in Fridley, Minnesota, “even if somebody steals the card, they can´t use it.”
All of this can work on a standard-size card, says Andrew Ho, CEO of SiPix Imaging in Fremont, California, because flexible electronic screens are cheap enough to distribute en masse, strong enough to survive wear and tear in your wallet, and so efficient that one small battery will last for three years.
THE ETA:
Alan Finkelstein, president of Innovative Card Technologies in Los Angeles, says that banks will start running pilot tests with these dual-factor security cards later this year. “If you´re one of the lucky ones,” he says, “you might get one soon.” Eventually the technology could lead to added features-future bank cards might flash your remaining balance or allow you to scroll through your last few purchases. -Gregory Mone
**PROTECT YOUR SECRETS **
Data thieves will soon have to crack the toughest lock imaginable: quantum weirdness
THE THREAT:
Losing private data to online eavesdroppers. When you send your banking information or other sensitive data over the Internet, it´s protected by cryptographic keys made from sequences of prime numbers. Right now it would take hackers days to crack these keys and break in. But the exponential rise in computing speed is shrinking that time, forcing researchers to devise new approaches to hack-proof communication.
THE SOLUTION:
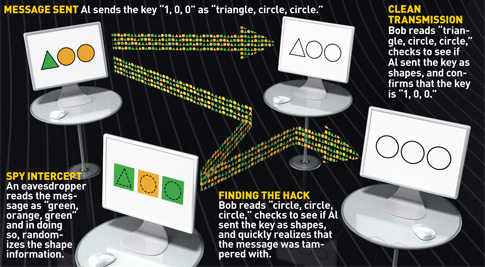
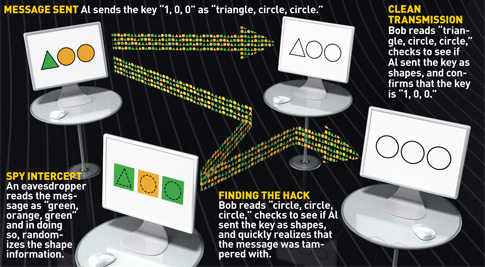
Use the built-in randomness of quantum theory to lock and unlock data, eliminating the possibility of a break-in. In an experimental network designed by Cambridge, Massachusetts”based BBN Technologies, a laser creates a key out of individual bits of light, or photons. It sends this key along a fiber-optic cable, and another optical device at the end of the line collects the photons and records the key. If the received photon sequence matches up with the one conveyed by the sender, the recipient is permitted to use this key to gain access to top-secret data over the network.
If an intruder tries to use a photon detector or other tapping device to snoop on the transmission, however, the eavesdropping attempt will irreversibly damage the photon sequence. This is because of the central rule of quantum physics: Observing impossibly small entities, like electrons and photons, necessarily alters them. “If someone´s trying to listen in, they change the quantum state of the photons as they´re going through the channel,” says Jonathan Habif, a physicist at BBN. “You can´t measure a quantum state without changing it.” Any such change is obvious, and alerts network administrators to the possibility of a break-in.
The high cost of specialized photon detectors means that quantum-secured networks will initially be reserved for classified government chats and high-value bank transfers. Still, Habif has wide-ranging goals for the future. “People will be able to use quantum cryptography for all kinds of transactions as the technology becomes cheaper and easier to implement,” he says. “This could become the standard in communications security.”
THE ETA:
When BBN first designed its prototype network, quantum cryptography could be used only to protect messages sent a couple miles or less. Last year, BBN researchers developed a more powerful single-photon detector that picks up even the faintest signals, increasing network range to more than 50 miles (new detectors in the works should extend it even further). Expect quantum-level security for consumers in about 10 years, after a test run of a few years in government settings. -Elizabeth Svoboda
**PROTECT YOUR FOOD **
Dinner tonight? A steak with certified “disease-free” DNA
THE THREAT:
Since 9/11, the threat of terrorists poisoning our food supply has diverted attention from more ordinary risks, like the dual threats of mad-cow disease and the E. coli bacterium. Food-safety scientists are bemoaning this development. E. coli sickens 73,000 Americans yearly, and in the U.K. mad-cow disease has killed 156 people, whose brains degenerated when they ate meat contaminated with the errant proteins that cause the disease.
THE SOLUTION:
To assure consumers that the rib eye they buy comes only from noncontaminated cows, Irish company IdentiGEN has developed TraceBack, the first-ever commercial DNA-fingerprinting technology for meat. The process starts at the farm or slaughterhouse, where cows are tested for pathogens. Once each animal receives a clean bill of health, a worker takes a sample of the cow´s blood, meat or hair, analyzes it for genetic identifiers known as single-nucleotide polymorphisms, and stores the information in a central database.
At the supermarket, butchers take another DNA sample and match it to the database. In this way, beef producers can prove that they packaged meat from a 100 percent disease-free cow. And if an errant pathogen is introduced at some point along the line-at a shipping facility riddled with E. coli, for instance-food-safety officials will be able to nail down the source of the outbreak within hours by retracing the journeys of infected animals. “Each product has its own inherent label. It´s like nature´s bar code,” says Ronan Loftus, IdentiGEN´s director of business development, who created TraceBack as a research fellow at Trinity College in the mid-1990s. “Once this system is in place, you can pull a package of meat off the shelves and access its entire history.” Consumers pay a barely noticeable premium for the “disease-free” sticker on their beef-on the order of pennies per pound-but come out ahead in peace of mind.
THE ETA:
After successful trials in Ireland and elsewhere in Europe, IdentiGEN opened its first North American offices last July. TraceBack certification stickers should start appearing in U.S. supermarkets within the next five years. -Elizabeth Svoboda
