

Roger Johnston is the head of the Vulnerability Assessment Team at Argonne National Laboratory. Not long ago, he and his colleagues launched security attacks on electronic voting machines to demonstrate the startling ease with which one can steal votes. Even more startling: Versions of those machines will appear in polling places all over America on Tuesday. The touchscreen Diebold Accuvote-TSX will be used by more than 26 million voters in 20 states; the push-button Sequoia AVC Voting Machine will be used by almost 9 million voters in four states, Harper’s magazine reported recently (subscription required). Here, Johnston reveals how he hacked the machines–and why anyone, from a high-school kid to an 80-year-old grandmother, could do the same.–Ed
The Vulnerability Assessment Team at Argonne National Laboratory looks at a wide variety of security devices– locks, seals, tags, access control, biometrics, cargo security, nuclear safeguards–to try to find vulnerabilities and locate potential fixes. Unfortunately, there’s not much funding available in this country to study election security. So we did this as a Saturday afternoon type of project.
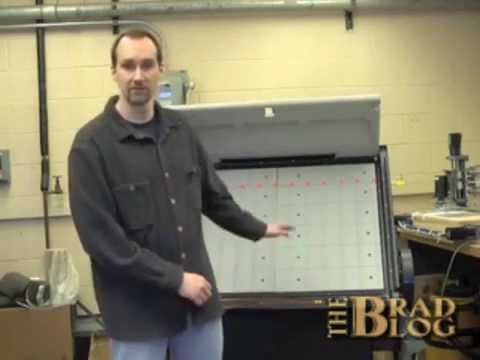
It’s called a man-in-the-middle attack. It’s a classic attack on security devices. You implant a microprocessor or some other electronic device into the voting machine, and that lets you control the voting and turn cheating on and off. We’re basically interfering with transmitting the voter’s intent.
We used a logic analyzer. Digital communication is a series of zeros and ones. The voltage goes higher, the voltage goes lower. A logic analyzer collects the oscillating voltages between high and low and then will display for you the digital data in a variety of formats. But there all kinds of way to do it. You can use a logic analyzer, you can use a microprocessor, you can use a computer–basically, anything that lets you see the information that’s being exchanged and then lets you know what to do to mimic the information.
I’ve been to high school science fairs where the kids had more sophisticated microprocessor projects.So we listened to the communications going on between the voter, who in the case of one machine is pushing buttons (it’s a push-button voting machine) and in the other is touching things on a touchscreen. Then we listened to the communication going on between the smarts of the machine and the voter. Let’s say I’m trying to make Jones win the election, and you might vote for Smith. Then my microprocessor is going to tell the smarts of the machine to vote for Jones if you try to vote for Smith. But if you’re voting for Jones anyway, I’m not going to tamper with the communications. Sometimes you block communications, sometimes you tamper with information, sometimes you just look at it and let it pass on through. That’s essentially the idea. Figure out the communications going on, then tamper as needed, including with the information being sent back to the voter.
We can do this because most voting machines, as far as I can tell, are not encrypted. It’s just open standard format communication. So it’s pretty easy to figure out information being exchanged. Anyone who does digital electronics–a hobbyist or an electronics fan–could figure this out.
The device we implanted in the touchscreen machine was essentially $10 retail. If you wanted a deluxe version where you can control it remotely from a half a mile away, it’d cost $26 retail. It’s not big bucks. RadioShack would have this stuff. I’ve been to high school science fairs where the kids had more sophisticated microprocessor projects than the ones needed to rig these machines.
Because there’s no funding for this type of security-testing, we relied on people who buy used machines on eBay [in this case the touchscreen Diebold Accuvote TS Electronic Voting Machine and the push-button Sequoia AVC Advantage Voting Machine]. Both of the machines were a little out-of-date, and we didn’t have user manuals and circuit diagrams. But we figured things out, in the case of the push-button machine, in under two hours. Within 2 hours we had a viable attack. The other machine took a little longer because we didn’t fully understand how touchscreen displays worked. So we had learning time there. But that was just a couple days. It’s like a magic trick. You’ve got to practice a lot. If we practiced a lot, or even better, if we got someone really good with his hands who practiced a lot for two weeks, we’re looking at 15 seconds to 60 seconds go execute these attacks.
I want to move it to the point where grandma can’t hack elections. We’re really not there.The attacks require physical access. This is easy for insiders, who program the machines for an election or install them. And we would argue it’s typically not that hard for outsiders. A lot of voting machines are sitting around in the church basement, the elementary school gymnasium or hallway, unattended for a week or two before the election. Usually they have really cheap cabinet locks anyone can pick; sometimes they don’t even have locks on them. No one signs for the machines when they show up. No one’s responsible for watching them. Seals on them aren’t much different from the anti-tamper packaging found on food and over-the-counter pharmaceuticals. Think about tampering with a food or drug product: You think that’s challenging? It’s really not. And a lot of our election judges are little old ladies who are retired, and God bless them, they’re what makes the elections work, but they’re not necessarily a fabulous workforce for detecting subtle security attacks.
Give people checking the seals a little training as to what to look for, and now they have a chance to detect a reasonably sophisticated attack. Do good background checks on insiders, and that insider threat would be much less of a concern. Overall, there’s a lack of a good security culture. We can have flawed voting machines, but if we have a good security culture, we can still have good elections. On the other hand, we can have fabulous machines, but if the security culture is inadequate, it doesn’t really matter. We’ve really got to look at a bigger picture. Our view is: It’s always going to be hard to stop James Bond. But I want to move it to the point where grandma can’t hack elections, and we’re really not there.
Read more about elections security here.
