We may earn revenue from the products available on this page and participate in affiliate programs. Learn more ›
You’re always online and you should be using a VPN. Sure, sometimes you’re on your work’s professionally managed network, but other times you’re at a coffee shop, using the Wi-Fi in an airport or hotel lobby, or even trying to return some emails while you wait in the doctor’s office. Getting more done in a day is admirable. Exposing more of your sensitive data in the process is not. Whether it’s because of malicious data packets or just unscrupulous marketing, joining an unknown network leaves you open to the unforeseen consequences of convenience. So the best way to protect your online communications is with a Virtual Private Network—a service that inserts a virtual connection between your device(s) and a public network and allows your data to funnel through servers that keep it secure. There are dozens if not hundreds of VPN providers out there offering to anonymize your online traffic, so we’ve collected recommendations on the best VPNs to make sure your business is only your business.
- Best overall: ExpressVPN
- Best for speed: Surfshark
- Best for reliability: NordVPN
- Best for ease of use: IPVanish
- Best for an upgradable free service: ProtonVPN
- Another great freemium VPN: Atlas VPN
How we selected the best VPN services
We gathered user testimonials from our staff and associates, their friends and family, and combed through specs and perspectives to bring you what we can confidently call a consensus on the best VPNs available. We’ve done the research so that you can know before downloading any VPN software or connecting to any VPN servers that you’re not exposing yourself rather than protecting yourself.
The best VPNs: Reviews & Recommendations
The best VPNs will offer convenience and consistency, but that may come at a price. While it’s tempting to try to save a little dough, when it comes to VPNs, you usually get what you pay for. Here are our recommendations that are worth the subscription.
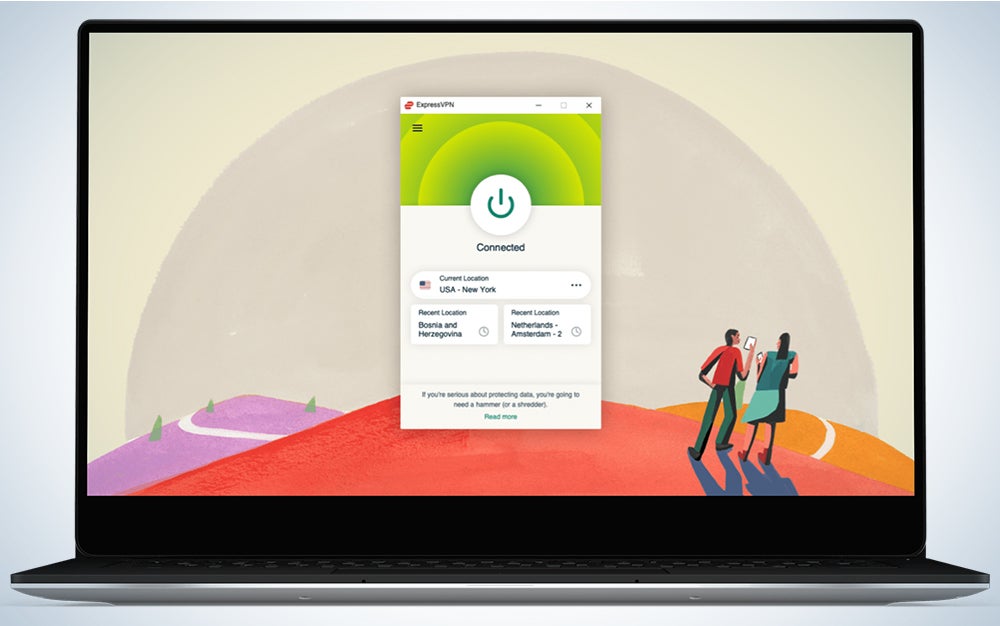
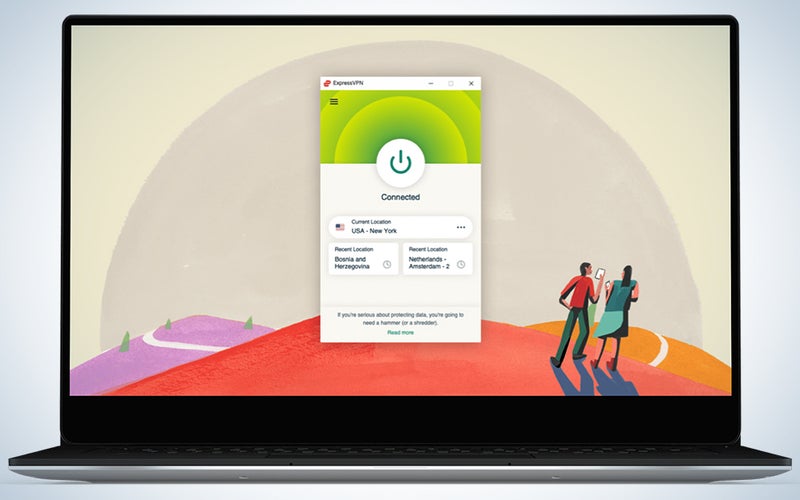
Best overall: ExpressVPN
ExpressVPN
Why it made the cut: ExpressVPN has literally everything one could ask for in a VPN service, including no-log connections, private DNS, and an easy-to-use and attractive app for every major platform.
Specs
- Over 30,000 IP addresses
- Over 3,000 servers in 160 locations in 94 countries
- Simultaneous Connections on One Account: 5
- Home Country: British Virgin Islands
- Platforms: Windows, Linux, iOS, Android, Router
- As low as $99 annually (with three additional free months when you buy the first year upfront)
- 30-day Money-Back Guarantee
Pros
- Tons of servers
- Reliable apps for every platform
- Great speed
Cons
- Expensive compared to competition
Our best recommendation goes to ExpressVPN, a service that has topped VPN best-of lists for the better part of the existence of VPNs. Located in the British Virgin Islands, ExpressVPN has proven its privacy bonafides; Turkish authorities once seized some company servers, but they found absolutely no logs of activity on the servers, backing up ExpressVPNs’ promises to customers. The country base is massive, perhaps even larger than necessary. Express constantly is updating its servers to maintain high speeds, though recently overall speeds have dipped quite a bit (perhaps due to increased work-from-home traffic demands during 2020). ExpressVPN also boasts the best customer service of any VPN, with a dedicated 24-hour chat function built right into its apps. While $99 a year is among the highest prices for a VPN on the market, you absolutely get what you pay for with ExpressVPN (and you can even pay with Bitcoin, if you’re crypto-inclined.)
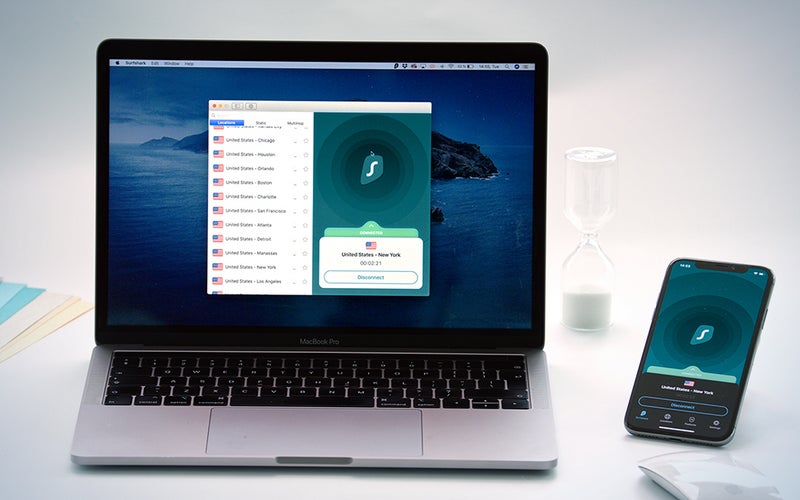
Best for speed: Surfshark
Surfshark
Why it made the cut: When you want to make quick, creative, and precise mixes, Serato DJ Pro’s hardware-software response is up to the task.
Specs
- Number of IP addresses not provided
- Over 3,200 servers in 160 locations in 65 countries
- Simultaneous Connections on One Account: Unlimited
- Home Country: British Virgin Islands
- Platforms: Windows, Mac, Linux, Android, iOS, browsers, Amazon Fire TV
- As low as $30 annually with a two-year plan
Pros
- Fastest speeds available
- Unlimited simultaneous connections
- Competitive pricing
Cons
- Smaller network
- No direct router support
Surfshark is a good choice for a combination of price and speed. While the company’s server base is smaller both in number of servers and number of countries, there’s still a pretty good swath of the world that is covered. Surfshark has a couple of extra features to help make you even more private, including Camouflage Mode, which masks the fact that you’re even using a VPN from the internet service provider you’re on, and Multihop, which routes your data through several countries in order to occlude your location. However, there is no annual plan available with Surfshark. To get their best price, you have to commit for two years; if you want to get a shorter plan, you get much less of a deal.
Best for reliability: NordVPN
NordVPN
Why it made the cut: A top name for years, Nord made a comeback after a security slip-up in 2019 with good, consistent speeds, broad support, and some extra security features for the most discerning user.
Specs
- Number of IP addresses not provided
- Over 5,200 servers in 62 locations
- Simultaneous Connections on One Account: 6
- Home Country: Panama
- Platforms: Windows, Mac, Linux, Android, iOS, browsers, Android TV
- As low as $50 annually with a two-year plan
Pros
- Dedicated IP addresses
- Long-standing reputation in the market
- Consistent speeds
Cons
- Despite no actual breaches, it has had some security concerns
Let’s get the bad out of the way: NordVPN ended up on a lot of blacklists two years ago when it was discovered that they had an unauthorized server access issue in 2018. Many people were concerned, despite extensive audits showing no personally identifiable information was at risk, because Nord didn’t disclose this breach themselves. However, because no sensitive data seems to have been available in the intrusion, it does back up Nord’s assertion that it doesn’t keep logs of user activity. On to the good, then: Nord offers some extra features at a competitive price, including a dedicated IP address (good for employers setting up system access solely for trusted users) and the ability to VPN into a Tor browser to double-down on anonymity in web traffic. These features are less for the lay user and more for IT professionals or enthusiasts who can fiddle their settings and know what they are doing, so they may not be particularly appealing to some. Overall, NordVPN is a service that offers a good service at a good price, a jack of all trades that doesn’t quite top any particular category.
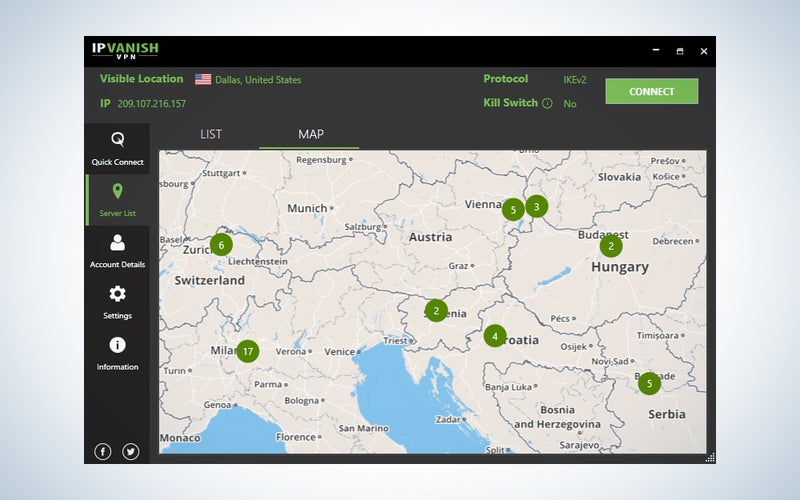
Best for ease of use: IPVanish
IPVanish
Why it made the cut: IPVanish is the easiest VPN to use for beginners, mostly because its interface is inviting and uncluttered.
Specs
- Over 40,000 IP addresses
- Over 1,600 servers in over 75 countries
- Simultaneous Connections on One Account: Unlimited
- Home Country: United States
- Platforms: Windows, Mac, Linux, Android, iOS, Amazon Fire TV, Chrome browser, router
- As low as $45 for the first year, and $90 annually thereafter
Pros
- Best user interface available
- Lots of support for multiple platforms
Cons
- US-based
- Lacks some features
IPVanish doesn’t quite kit out the features that its competition does, which makes it tough to recommend as our #1 VPN service. However, what the others on this list could learn from IPVanish is how to make the user experience more enjoyable and clear. IPVanish’s interface gives clear information in text and graphs—including speed measurements, data transfer amounts, visible location and IP, and other information that you often have to dig to find in the competition. For some, that’s enough to push IPVanish into pole position. Where it falters is the depth of options, especially if you want to use a VPN for business. There’s no option for a dedicated IP address, even at an additional fee. While many platforms are covered by IPVanish’s apps, there aren’t too many additional security features that IPVanish offers. The interface is simple and so, too, is the service in many ways. Additionally, IPVanish is based in the United States, which means that even with privacy measures in place on the data, the company itself might be forced by law to reveal some user information, while British Virgin Islands companies, for example, would not be. This US base may also limit IPVanish’s ability to unlock geolocked content.
Best for an upgradable free service: ProtonVPN
ProtonVPN
Why it made the cut: Really strong across the board, despite having a small server base, ProtonVPN is very transparent and community-focused, with consistent data audits and an open-source approach. And there’s a free (though speed-restricted) option.
Specs
- Number of IP addresses not provided
- 1,326 servers in 55 countries
- Simultaneous Connections on One Account: Up to 10 (1 on free tier, 2 on basic tier)
- Home Country: Switzerland
- Platforms: Windows, Mac, Linux, Android, iOS, Chromebook, Android TV
- As low as $80 annually on a two-year plan for all features
Pros
- Free tier
- Community-focused
- Transparent
Cons
- Expensive for its offerings
Remember how up top I said to avoid free VPN service? There’s one exception and that’s ProtonVPN’s admittedly extremely limited free tier. More a chance to test the service out than a long-term option, the free tier from this Swiss privacy provider offers users access to 23 servers in three countries on only one active connection, with a speed limit in place. There’s also a cheaper ($48 annually) “basic” tier with two simultaneous connections and 350+ servers in 40 countries. Proton, of course, promises no logging of your data, and the company’s transparency and community/journalist/activist information freedom focus backs up those claims. ProtonVPN is constantly doing data audits to prove the anonymity and security of its service. It also offers slightly more secure mobile apps than a lot of competitors.
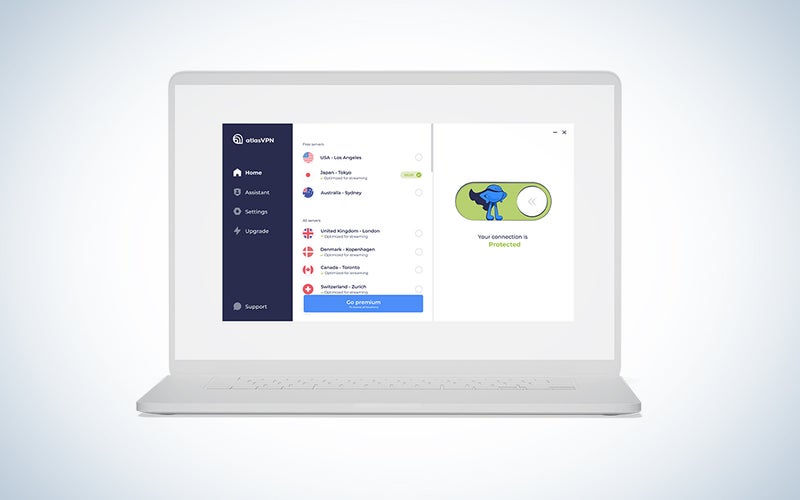
Another great freemium VPN: Atlas VPN
Why it made the cut: Atlas VPN unlocks many sites without logging your activities, offering a lot of security features for little (or no) cost.
Specs
- Number of IP addresses not provided
- Over 750 servers in 27 locations
- Simultaneous Connections on One Account: Unlimited
- Home Country: United States (Delaware)
- Platforms: Windows, macOS, iOS, Android
- Three free locations with no speed limits and unlimited devices
- Premium plans low as $49.99 for three years, with a 30-day Money-Back Guarantee
Pros
- Robust no-logs policy
- 4K and P2P support
- Strong encryption
Cons
- Free tier has a data cap
- Fewer servers than other providers
Using the blazing WireGuard protocol (as well as the less speedy IKEv2), Atlas VPN offers fast for free. AES-256 encryption combines to make sure that whatever you’re using that speed for (whether that’s streaming, torrenting, or other) remains secure. Now part of Nord Security, the company is based in the United States (Delaware), which has possible law-enforcement implications not faced by other countries, but the company is transparent and stresses its no-logs policy. You don’t have to sign up for an account to use the free service, and information that can trace usage to you is kept to a bare minimum. SafeSwap helps change your IP regularly, and a kill switch blocks all internet if a connection becomes unprotected. Free accounts have limited locations and a daily data limit, plus some geoblocking limitations, but inexpensive plans drop those.
What to consider when picking the best VPN services
The main use of a VPN service is to create an encrypted data tunnel between you and the sites you visit while on public networks. The vast majority of Wi-Fi networks in public retail, transportation, etc.—even if they are password protected—are not particularly secure because increased authentication makes them very difficult to keep quickly accessible by customers while ensuring security. This means that someone on the same network can often easily see what activity you are engaging in, up to and including in worst-case scenarios seeing what passwords and personal data you may be entering in sites. A VPN creates a connection to a dedicated server that encrypts your communications before returning them to the network you’re using, shielding that data from prying eyes. It’s honestly a layer of security that everyone needs at this point. While being an internet user is inevitably going to mean trusting your data to someone else, the fewer people you trust it to, the better. Once you download, install, and connect through a trustworthy VPN, you’re minimizing your risk.
I work from home. Is a VPN useful?
Have you spent much time in the configuration panels of your service provider’s router? If so, congratulations, you’re a glutton for punishment, because those things are not easy to translate or navigate. Seeing as many folks don’t go to the painstaking steps of exploring the backend of computer hardware to maximize security, a personal VPN is a smart choice even at home. Especially as more and more people work from home, a VPN is an excellent way to ensure that sensitive data is treated as such. While a VPN isn’t terribly necessary if you’re just streaming entertainment (unless you want to change the location that services or websites see you as connecting from, for reasons we explain below), some work-from-home set-ups actually require a VPN when accessing an enterprise network.
Are VPNs safe to use?
Every access point provides just that: access. And with access comes risk. Because the VPNs grab your data before you send it, they do in some ways know what you’re doing even if the public network you’re connected to does not. Many free, no-name VPNs are essentially backdoors into your system and are more dangerous than simply using public networks without a VPN. Even the best free service isn’t running as a public service; they will be making money off your data in some way. However, the VPNs on our list are all regarded as reputable and secure, often using double-blind methods of encryption with no data storage, so that the information passing through their servers is unknowable to the VPN company itself.
What else can I do with a VPN?
In addition to encrypting your communications, a VPN can spoof the location of your computer, phone, or tablet, which means that you can appear to be a user from another country. This creates a grey area with many streaming and online services, where you can either access them from regions in which they’re not technically available or get around geolocked content in your region. For example, the Netflix library while logged in from a UK server may feature different content than the one while logged in from a US server. While this is a tempting reason to get a VPN for many, keep in mind that many of the streaming services don’t want users to have this ability and will ban IP addresses that they detect as being owned by VPNs or may restrict content to only that which is available in all regions. While there is very little evidence of it happening, the streaming companies even have the right to terminate your service if they detect you accessing their content in a manner that goes against the terms of service (which I’m sure, like all of us, you spent hours reading before you signed up to binge “Breaking Bad”). With all that in mind, use a VPN for Netflix, etc., at your own risk.
So, what should I look for in the best VPN?
In short, four things: privacy, reliability, speed, and versatility. Privacy means that the VPN connection is secure and the VPN service itself is not skimming or viewing your data. Reliability means their servers are available and functioning whenever they need to be used. Speed is tricky, as rerouting your data will always slow down your communications. For example, if you wanted to play online games while still connected to your VPN, a worse service may result in increased lag, while a good one will be less discernibly slower (though it will be slower than an unfiltered connection). Finally, versatility looks at the number and locations of servers, the types of devices the service can be used on, and the additional privacy tools that the service provides.
Some terms you need to know
Network security can get very technical very quickly. While we can’t go into the nitty-gritty, there are some basic terms that, once you’re familiar with, will help you make your decision.
Internet Protocol, or IP, addresses are the identifiers for the location of your network. With a normal IP, your local router is often the determiner of your IP and will let websites and apps know where you are geographically. VPNs mask your IP by giving the IP address of their servers instead of your router, showing you as being located anywhere in the world you want to be. A dedicated IP address is one that doesn’t change every time you log in or use the service and is available only to trusted users. This is good for work security if your company needs you to log in from the same location every time you work remotely but you still want the peace of mind a secure VPN provides.
DNS is short for Domain Name System. DNS marks specific devices or subnetworks connected to an IP address. Every location on the Internet, including your local network connection, has an IP address. Typically, a named location (such as popsci.com) isn’t a “real” location on the internet. Instead, DNS is able to translate that text domain into an IP address, allowing access to that network or website through the alphabetic domain name. Some lesser (not recommended here) VPNs can leak DNS information even if they don’t leak IP information, which allows a partial identifier of your traffic. All the services here keep DNS information secret very effectively and some even offer an extra layer by having private DNS for individual accounts.
A Tor browser is an extremely secure and anonymous web browser. While Tor browsers have a bad reputation in the media, in reality they’re just an extra layer of security and anonymity. They are modified versions of the open-source Mozilla browser that go through the Tor network before connecting to the larger web, creating another layer of security and network masking between you and the end connection. The function of the Tor network and a Tor browser is to make all users on their network look like the same user, shielding any personally identifiable information about your network or device. Some of the VPNs listed will allow you to VPN into the Tor network through a Tor browser so that your web traffic is doubly anonymized.
FAQs
Q: Is VPN illegal?
In most countries, using VPN features is completely legal. However, this is not true in every single country as some nations regulate and limit internet use more than others. In the United States, rest assured that you are not doing anything illegal by using a VPN. However, using a VPN to access content on services (even ones you pay for) that is not intended for your region is a violation of the terms of service. While none of the major streaming companies have gone after users in this way, they have the right to terminate your service if they find you are using a VPN. More likely they will simply block the VPN servers as they discover them, creating a cat-and-mouse game between the VPN and streamers for content to be accessible.
Q: Do I need antivirus if I have a VPN?
Yes, you still need to use antivirus checks on your computer even if you’re using a VPN. A VPN helps protect your data from being accessed but it doesn’t help if you access infected files. Some VPNs will offer additional antivirus services on files, but it’s always best to do no-less-than-weekly checks of your hard drive for any questionable data.
Q: Can you be hacked through a VPN?
All of the services listed above are secure and reliable and will make your system safer. Nothing is infallible, but some things are more trustworthy than others. Free VPNs from disreputable sources, no matter the promises, are absolutely going to put your system at risk. If a company is offering to sort your data for free (and not trying to upsell you on a service like ProtonVPN), they’re making money off that data somehow. It might be innocuous like direct marketing, but it could be straight-up identity theft. Avoid free VPNs, period.
The final word on selecting the best VPNs
- Best overall: ExpressVPN
- Best for speed: Surfshark
- Best for reliability: NordVPN
- Best for ease of use: IPVanish
- Best for an upgradable free service: ProtonVPN
- Another great freemium VPN: Atlas VPN
While ExpressVPN gets our highest recommendation, any of the above services are great options. A VPN is a necessary security precaution in today’s networked world and the bonus benefits are numerous. Spending $30 to $100 a year may seem like an unnecessary expense, but all it takes is one time that you should have had a VPN to make you wish you did. If you live a good portion of your life online—and let’s be honest, anyone reading this probably does—a VPN is a necessity, not a luxury.
Why trust us
Popular Science started writing about technology more than 150 years ago. There was no such thing as “gadget writing” when we published our first issue in 1872, but if there was, our mission to demystify the world of innovation for everyday readers means we would have been all over it. Here in the present, PopSci is fully committed to helping readers navigate the increasingly intimidating array of devices on the market right now.
Our writers and editors have combined decades of experience covering and reviewing consumer electronics. We each have our own obsessive specialties—from high-end audio to video games to cameras and beyond—but when we’re reviewing devices outside of our immediate wheelhouses, we do our best to seek out trustworthy voices and opinions to help guide people to the very best recommendations. We know we don’t know everything, but we’re excited to live through the analysis paralysis that internet shopping can spur so readers don’t have to.
Related: Browsers with VPNs