Duplication at a Distance
A new reason to keep looking over your shoulder
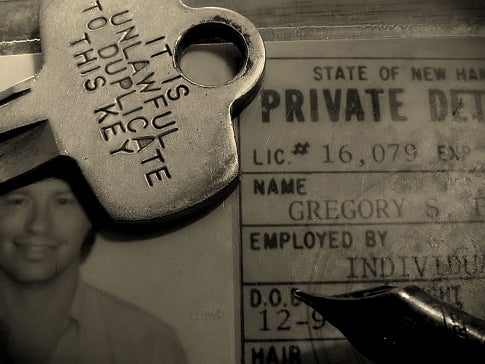
Stefan Savage, a professor at UC San Diego’s Jacobs School of Engineering, can duplicate a key for you — using just a photo of the original. As part of an experiment in security with students, the computer science prof took a photo of a key with a telephoto lens mounted on the roof of the UC campus 200 feet away, and used it to create a duplicate of the key.
The UC team created a software program called Sneakey that can re-create the “biting code” of a key. This code, which is quite simple compared to the passcode needed to unlock, say, a wireless network or encrypted hard disk, examines the indentations of a standard key, which usually has only five or six cuts. The software uses this to output a copy of the biting code, which can be used to create a new key. A “control” key representing common key brands helps to fill in the missing details.
Savage says the proof of concept shows how computers and software can aid criminals in compromising physical security — such as padlocks and doors — just as easily as corporate networks and computers. While the concept of using computer images to re-create an object on the computer is not new, the simplicity of keys’ biting codes points to a trend where hackers can more easily break physical security constraints — using easy-to-create software, a PC, and a cell phone camera.
The team also pointed out that pictures of keys are readily available on the Internet. Of course, physical keys are quickly becoming old tech. Many newer cars use PATS (passive anti-theft system) keys, whose chips cannot be duplicated by this method.