Anatomy of a Hack
After video site Revision3 was attacked and brought down over the weekend, a little digging revealed a surprising perpetrator
Over the long weekend, the servers of the Internet TV site Revision3.com were brought down by what is called a “denial-of-service” attack (DoS)—one of the most common methods used to disrupt the operations of a Web site or server by flooding it with an overload of simultaneous connections. These attacks are not uncommon, but in a fascinating blog post written by Revision3’s CEO Jim Louderback today, he reveals that the source of this particular attack was not a pimply basement hacker with a grudge, but a major anti-piracy organization called MediaDefender whose clients include all the major entertainment companies and the RIAA. The hitch? Revision3 is a perfectly legitimate business that does not deal in pirated content.
Revision3 uses the popular BitTorrent protocol to distribute the video files for its own high-defintion, Web-only shows. BitTorrent works by harnessing users’ own computers spread across multiple networks to deliver large files in bite-sized chunks, so it’s an easy and efficient way to deliver a multi-gigabyte HD video file without hogging the bandwidth of a single delivery server. While the protocol itself is perfectly legal, it can of course be used to easily and illegally distribute pirated movies, music and software, which is where MediaDefender comes in.
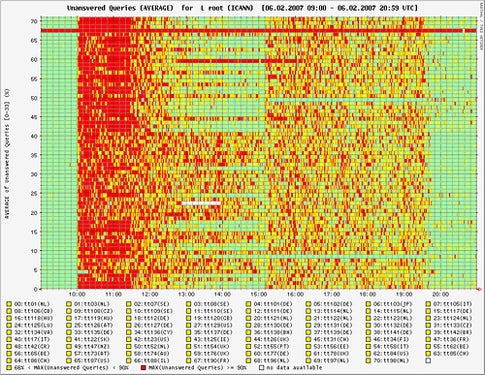
Organizations like the RIAA come to MediaDefender to intentionally disrupt illegal BitTorrent servers using every tool in the hacker’s book, including DoS attacks. In Revision3’s case, their own BitTorrent server had a security hole that allowed pirates to use it to secretly distribute unauthorized files. When MediaDefender became aware of the loophole, they began their efforts to disrupt its operations, which eventually led to the DoS attack which brought down not only Revision3’s BitTorrent server, but its entire public-facing Website and its corporate email system. Anyone who tried to download their shows over the long weekend (and view their revenue-generating ads) was met with a blank screen.
The thing is, attacks like these against legitimate businesses are illegal. Revision3 states that “the FBI is looking into the matter,” so we shall see how it plays out for the legality of MediaDefender’s admitted attack. In the mean time, Louderback’s post is not only an intriguing Internet-era whodunnit, but also an enlightening and well-written primer in plain English on how these types of attacks work. Fascinating stuff and well worth the read.
Read More: Inside the Attack that Crippled Revision3